APT 010
Also known as: Menupass Team, Cloud Hopper
Suspected attribution: China (Ministry of State Security)
Target sectors: Construction and engineering, aerospace, and telecom firms, and governments in the United States, Europe, and Japan
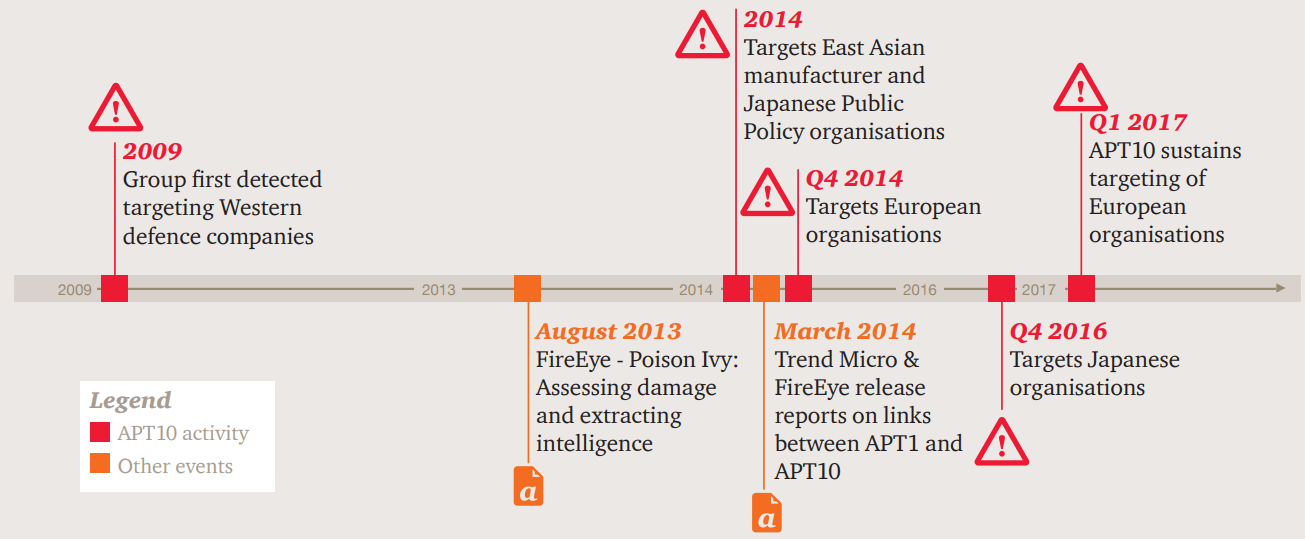
Overview: APT10 is a Chinese cyber espionage group that FireEye has tracked since 2009. They have historically targeted construction and engineering, aerospace, and telecom firms, and governments in the United States, Europe, and Japan. We believe that the targeting of these industries has been in support of Chinese national security goals, including acquiring valuable military and intelligence information as well as the theft of confidential business data to support Chinese corporations.
Associated malware: HAYMAKER, SNUGRIDE, BUGJUICE, QUASARRAT
Tools used: PlugX – a well-known espionage tool in use by several threat actors RedLeaves – a newly developed, fully-featured backdoor, first used by APT10 in recent months
Attack vectors: This recent APT10 activity has included both traditional spear phishing and access to victim’s networks through managed service providers. (For more information on infection via service providers see M-Trends 2016). APT10 spear phishes have been relatively unsophisticated, leveraging .lnk files within archives, files with double extensions (e.g. [Redacted]_Group_Meeting_Document_20170222_doc_.exe) and in some cases simply identically named decoy documents and malicious launchers within the same archive. In addition to the spear phishes, FireEye ISIGHT Intelligence has observed APT10 accessing victims through global service providers.