How a cyber attack works
Theory and practical samples
A very sad example has happened to the German Parlaiment recently. The network (Windows based) has now to be rebuild as the attackers managed to get hold of the kerberous hash and get them a "golden ticket".
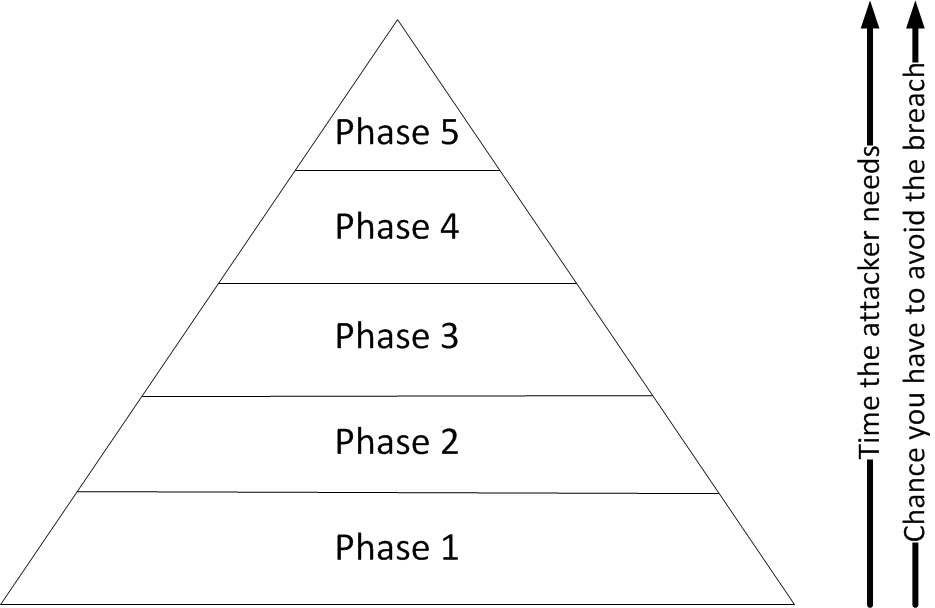
Let me draw a theoretical and a bit prictical excample of how such an attack/breach could work.