DigitalSide is giving a free MISP-feed to the community
Davide Baglieri has build a service to enrich you own MISP data with valuable information. During the last sync, there were 1096 events.
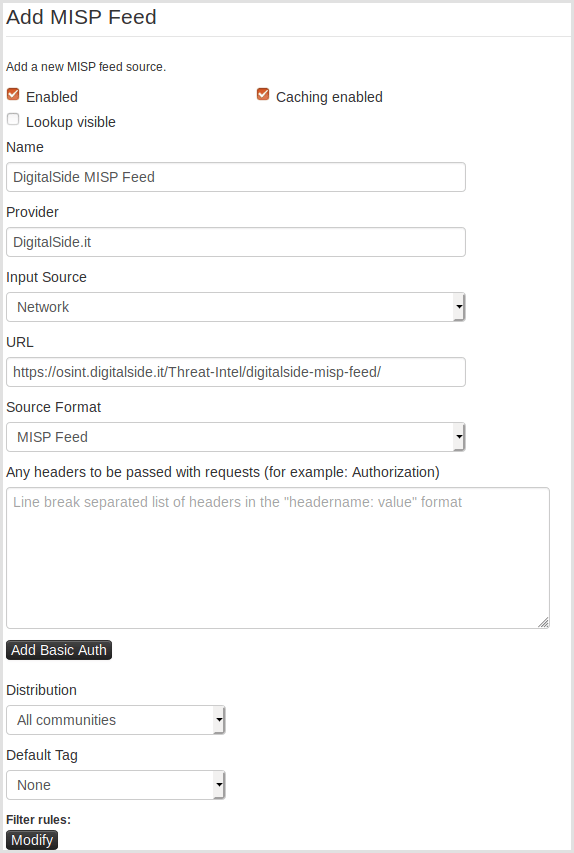
Checkout the HowTo or just add https://osint.digitalside.it/Threat-Intel/digitalside-misp-feed/ as a new feed.
This repository contains a set of Open Source Cyber Threat Intellegence information, monstly based on malware analysis and compromised URLs, IPs and domains.
The purpose of this project is to develop and test new wayes to hunt, analyze, collect and share relevants sets of IoCs to be used by SOC/CSIRT/CERT with minimun effort.
Sharing formats - [MISP] - [STIX2] - [CSV] - [TXT]
Three formats are availables to download the reports:
- MISP feed and events (retention: 7 days) - [GO TO]
- Structured Threat Information Expression - STIX™ v2 (retention: 7 days) - [GO TO]
- Comma Separated Values (retention: 7 days) - [GO TO]
- IoC lists of uniques indicators in squid like format (retention: 7 days) splitted in:
The majority of the informations are stored in the MISP data format. So, best way to collect data is subscribe the Digitalside-misp-feed. All sharing formats are based on MISP export format. All reports in any format can be consumed by any up-to-dated MISP instance.