Harddisks
As we have now forensicly discovered and analysed the active parts of the machine, it's time to take care of things that might only be available in an offline state.
What ever you start doing with a forensic investigation of a memory device (harddisk/USB-stick, etc.), NEVER attach it to a running machine without ensuring to have any write mode disabled.
This means, only a sophiticated hardware peace will do the job. Even if you just connect the forensic harddisk to a windows machine without actually accessing it, still timers will be changed and taint all you further effort as you can not prove who has made the change.
I'm investigating the behaivour of Linux in above terms, but unless I'm 120% sure of a way to achieve a completly passive connection through linux, I would not recomend.
For non-profesional actions, I've had good experience with the Sharkoon DriveLink Combo USB3.0. It has a hardware write block and does not cost to much. [50 Euro at Amazon]
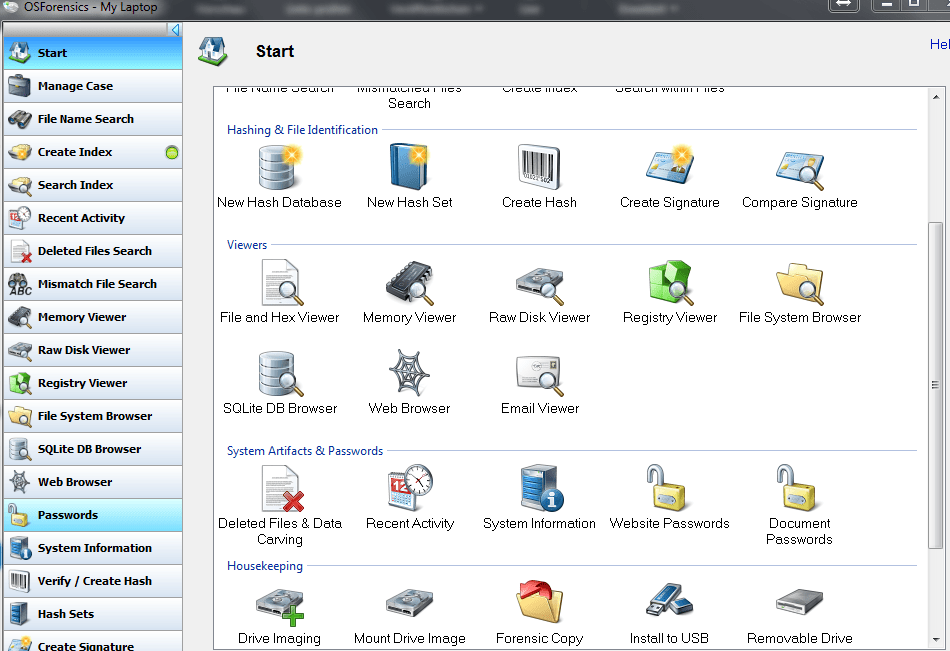
A very handsome tool for investigating (the copy of) your forensic device is OSForensics which does a very good job (at first and second view) even in it's free version. The questions of who did what on the machine, this tool seems to be ideal.
If you download the supplied hashes, you can even check on changes made to the basic OS files.
As long as you work with the copy of your forensic device, you can't spoil anything anyway. So give it a try.