2019 content
This is the raw content that will be put into the Cybernews blog.
Week 52
36c3 - FinFisher ev. broke the law
As the software was reversed by Thorsten Schröder and Ulf Buermeyer, it showed hard evidence that the Turkey espionage software was crafted by the germen company finfisher at a time where the export of such thing was already forbidden by german law.
Together with Reporter Without Borders (ROG), the European Center for Constitutional and Human Rights (ECCHR) and netzpolitik.org, the GFF has filed criminal complaints against the managing directors of FinFisher GmbH, FinFisher Labs GmbH and Elaman GmbH.
There are urgent indications that the Munich company conglomerate sold the spy software FinSpy to the Turkish government without the approval of the German government and thus contributed to the surveillance of opposition figures and journalists in Turkey.
See the whole story at media.ccc.de
Week 50
Week 49
My Linux Forensic Cheatsheet

I've started another cheatsheet in the term of a brainstorming action for finding Linux artifacts within a forensic discovery.
This will be an endless "work in progress" as I don't expect to ever find every spot to look at. But, hey, prove me wrong and help to extend the list. :-)
Week 48
Vitaly Kamluks bitscout to forensically inspect a remote customers machine
Check out my article of a great tool to create you own customizable ISO boot image to get onsite via a vpn tunnel and acquire the customers machine for forensic investigation.
My Windows Forensic Cheatsheet

When ever I look at a forensic evidence I'm afraid to miss some spot and start going over and over it, just to be sure not to have forgotten something very important.
Well. this is why I started my cheat sheet to have a kind of list to tick off.
Join me in "ticking off" when ever you do some similar stuff.
Week 47
Conrad Electronics: Elasticsearch DB with 14 mio. customer records compromised
A big german electronics company (being a supplier for big german companies) has lost his customer data to foreign intruders.
As per the press statement, it included 14 million customer records (but NO passwords and credit card data) that where accessible over the last months to unauthorized attackers.
As this includes names and email addresses, you should be very warily with mails from conrad.de, as this leak could be used (at least) for phishing attempts.
The original (german) statement from Conrad can be found here.
Meetup 11.Dec.2019: Cyber Incident Handling Game, hosted by Dr. Andreas Rieb and Marcus Pauli
On peoples demand of the past similar event, we will host another table-top game. Please come an join us in great talks and a fantastic area of our showroom. Just sign up with the meetup here.
In the Cyber Incident Handling Game, led by dr. Andreas Rieb, the participants in working groups of approx. 6 persons are confronted with a cyber security incident. The goal is to record this incident as part of IT emergency management and to plan suitable measures. These include u.a. Measures to assess the situation, develop options for action, business continuity, restart and follow-up.
Here, both technical measures as well as cross-IT measures such as public relations or reporting to law enforcement agencies in the foreground.
Come and "play" with us?
The Cyber Incident Handling Game is conducted in German.
If you did not include your full name and surname in your Meetup Profile, please also email us at contact.cybersecurity@airbus.com with the subject "Cyber Incident Handling Game".
We look forward to you!
Week 44
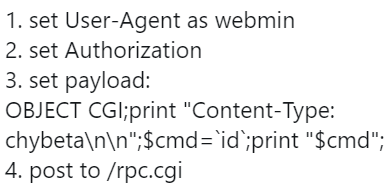
Fast scan for CVE-2019-9798
Rick Wanner wrote a simple script to combine masscan and rdpscan to detect BlueKeep CVE-2019-0708
Check this out:
#!/bin/bash
#create a date parameter for the various files so scans run on different dates don't overwrite each other.
TDATE=`date +%Y%m%d`
# put your IPs or IP ranges you would like to scan in scan_ips.txt
# this will be used as the input to masscan
# the output file is rdpips-<DATE>.txt
echo "executing masscan"
/usr/bin/masscan -p3389 -v -iL scan_ips.txt > rdpips-$TDATE.txt
#the output from the masscan will be used as the input to rdpscan
#the output file will be RDP_results-<DATE>.txt
echo "executing rdpscan"
rdpscan --file rdpips-$TDATE.txt > RDP_results-$TDATE.txt
Week 42
ZDNet: Simjacker attack exploited in the wild to track users for at least two years
Catalin Cimpanu for Zero Day wrote a cool article about SIMJacker being used for the last two years.
The reader that might not have heard about this vulnerability of millions of cell phones, may be interested in below description taken from a very detailed report coming from AdaptiveMobile Systems:
The main attack observed involves two stages:
1) Attack Stage: An SMS ‘Attack Message’ is sent from an attacker to a victim phone number
The Attack Message executable primarily instructs the SIM Card to request Location Information – the current serving Cell-ID of the handset and the IMEI from the Handset, and send the Location and IMEI from the Handset in a 2nd SMS. These instructions are in the form of a series of SIM Toolkit (STK) instructions, which the SIM Card will run to obtain the relevant information.
2) Exfiltration Stage: An SMS ‘Data Message’ is sent from the Victim Handset to a Recipient Phone Number – i.e. the Exfiltration Address.
This activity is not noticeable by the Victim – there is no indication on the handset
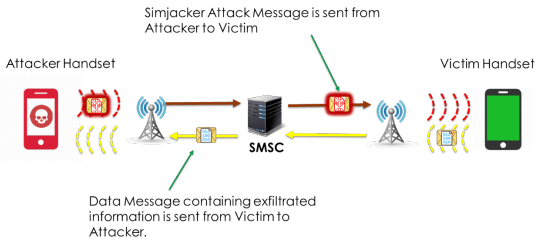
Note: This diagram is for illustration. Often the Attackers send the Data Message to a different Recipient Phone Number than that which originated the actual attack.
My personal conclusion:
Despite the information disclosure and GPS tracking ability an attacker has on the victims device, he can use the S@T browser to download/install (in combination of other vulns) any stuff he likes on the device. But think of the "low hanging fruites" of:
- Fraud Applications
- Advanced Location Tracking
- Assistance in Malware Deployment
- Denial of Service
- Information Retrieval
- Misinformation
By the nature of the technology, everything is done with zero-security.
Exploring the MQTT Protocol with ESP8266
Using an RPi as the MQTT broker. We'll explore two-node communication as well as LWT messages (last will).
Story
In any IoT project we have a number of unique requirements and restrictions. The communication strategy to connect devices and send data between them is critically important.
In this guide we will explore a powerful, simple and lightweight messaging protocol over the wire: MQTT
Main Features
- Data agnostic: you can use it to send sensor data, images or even OTA (over the air) updates
- Lightweight and bandwidth efficient: smallest frame is only 2 bytes long
- Per-queue QoS levels
- Runs on top of the TCP/IP stack, so you can use it to encrypt the data with TLS/SSL and to have a secure connection between clients
- Simple to develop: clients exist for all operating systems and programming languages
- Central broker: different devices can communicate with each other without having to worry about compatibility
- Session awareness: provides an identity-based approach for subscriptions
- Flexible subscription topics using single-level and multi-level wildcards
Week 37
"Heartbleed" @ Marcus
![]()
Sorry for being so silent the last view weeks, but I had an heart attack and still need some time to recover. - But cyber time does not stand still so I still have collected some news worth knowing.
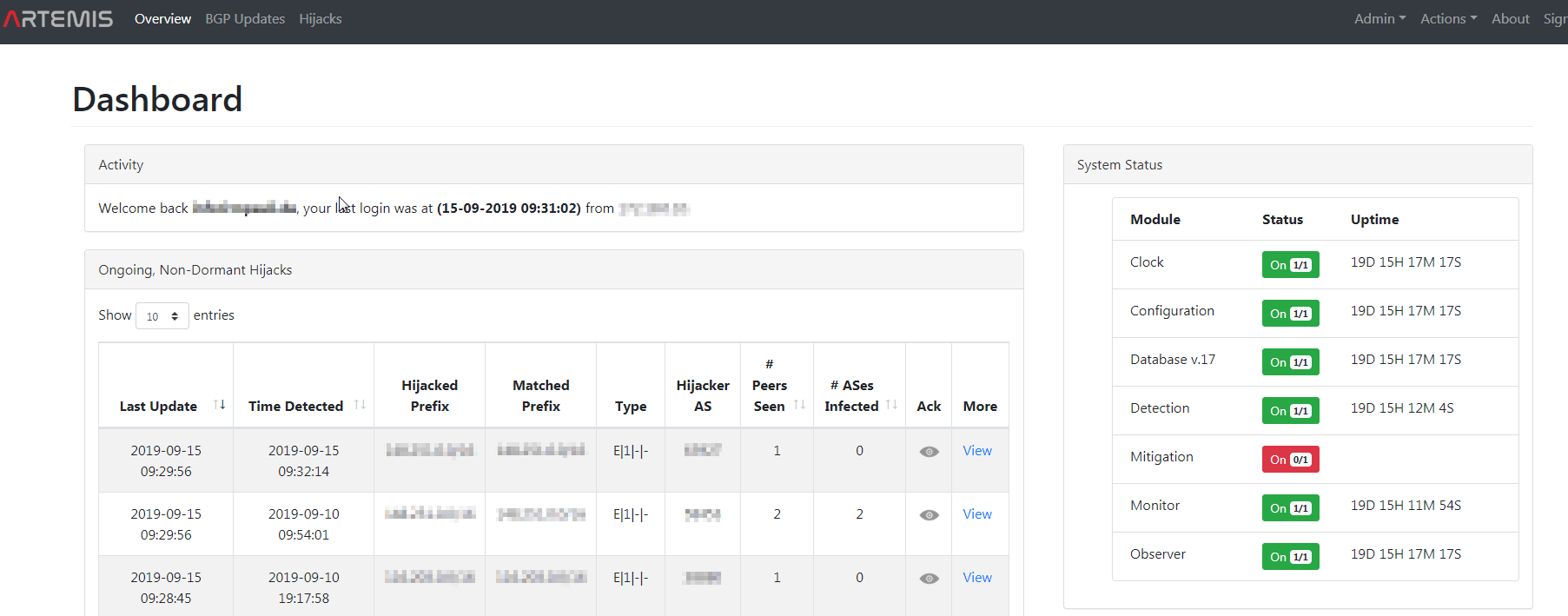
Artemis: BGP-Hijack monitor
![]()
FORTH-ICS-INSPIRE from Greek is providing the community with a personally long awaitet tool to monitor BGP-Hijack attempts of configurable networks.
Features:
- Real-time monitoring of the changes in the BGP routes of the prefixes originated by the AS running ARTEMIS.
- Real-time detection and notifications of BGP prefix hijacking attacks/events of the following types (please refer to the attack taxonomy in our ARTEMIS ToN paper):
- exact-prefix, type 0/1, any data plane manipulation
- sub-prefix, any type (0/1/-), any data plane manipulation
- squatting attacks, type 0 (others are N/A), any data plane manipulation
- policy violations (route leaks) due to long paths towards no-export prefixes
- Automatic/custom tagging of detected BGP hijack events (ongoing, resolved, ignored, under mitigation, withdrawn, outdated and dormant).
- Manual or manually controlled mitigation of BGP prefix hijacking attacks.
- Comprehensive web-based User Interface (UI).
- Configuration file editable by the operator (directly or via the UI), containing information about: prefixes, ASNs, monitors and ARTEMIS rules ("ASX originates prefix P and advertises it to ASY").
- Support for both IPv4 and IPv6 prefixes.
- Support for both mobile and desktop environments (UI): sample screenshots.
- Support for docker-compose (local deployment) and Kubernetes (helm charts).
- Support for multiple modes of operation (passive monitor/detector, active mitigator, etc.).
- Modularity/extensibility by design.
- CI/CD.
I created a PoC on my environment to monitor my providers AS. Looks pretty amazing.
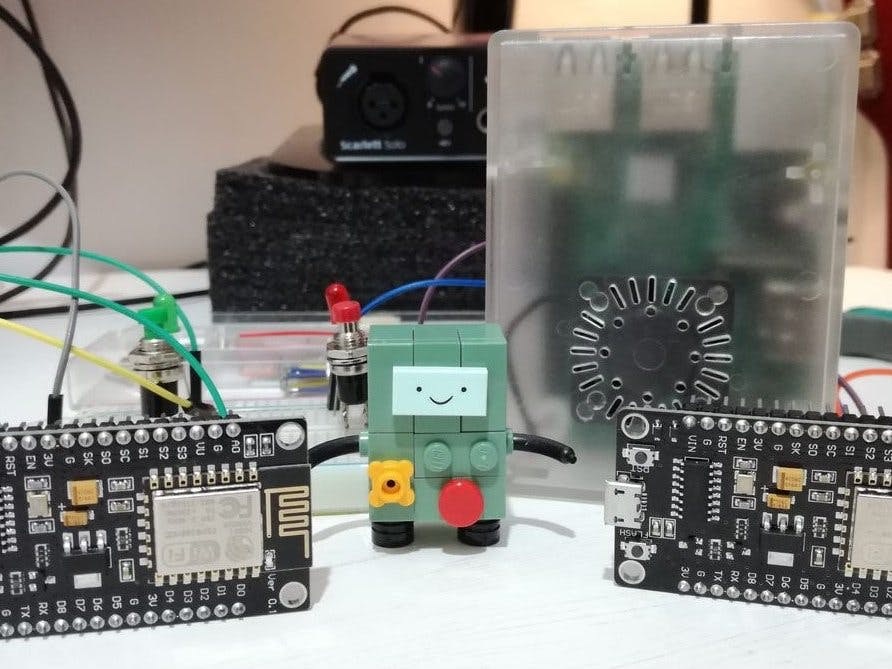
Animated workflow of the Enigma machine
Tom MacWright is showing the animation of how the Enigma works. This is a "must see" of an excellent work.
Portable ATM skimmer card detector
Cameron Coward has written an article about a portable skimmer card detector for ATMs.
So if you were ever unsure if everything is alreight with the ATM your using, use this little 35$ device to see if your card data is being copied away. (watch the legal situation of your country)
Checkout hackster.io not only for this cool gadget.
Week 31
Visualize windows eventlogs with LOGONTRACE
Thx to JPCERTCC/LogonTracer
While I was busy doing windows event log anaysis the past days, I came across a very cool tool to visualize the different WinEvents with LogonTracer of the JPCERT.
LogonTracer is a tool to investigate malicious logon by visualizing and analyzing Windows Active Directory event logs. This tool associates a host name (or an IP address) and account name found in logon-related events and displays it as a graph. This way, it is possible to see in which account login attempt occurs and which host is used.
This tool can visualize the following event id related to Windows logon based on this research.
- 4624: Successful logon
- 4625: Logon failure
- 4768: Kerberos Authentication (TGT Request)
- 4769: Kerberos Service Ticket (ST Request)
- 4776: NTLM Authentication
- 4672: Assign special privileges
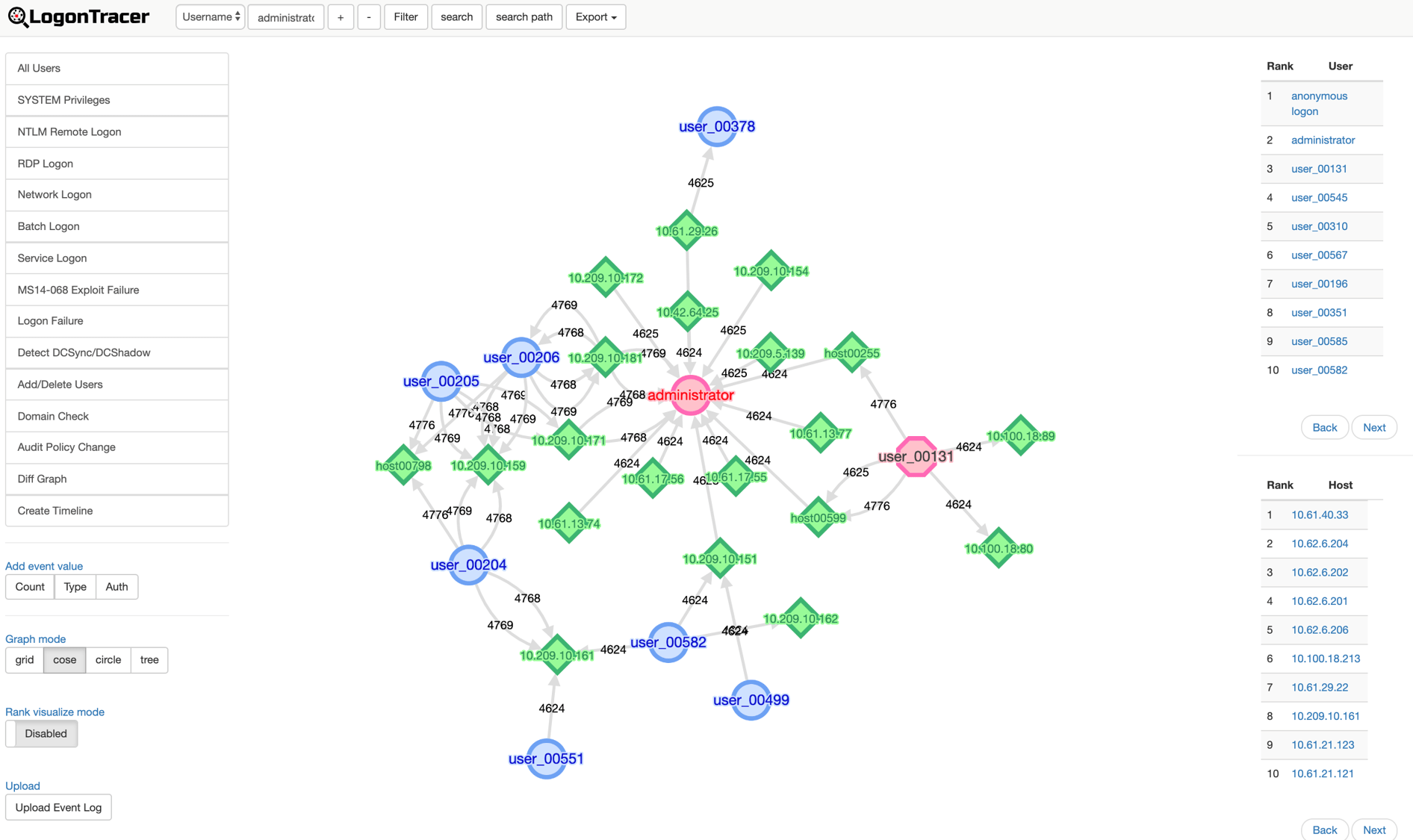
While using a docker image, the installation is very easy, so is the use. - Give it a try.
$ docker run \ --detach \ --publish=7474:7474 --publish=7687:7687 --publish=8080:8080 \ -e LTHOSTNAME=[IP_Address] \ jpcertcc/docker-logontracer
SYSMON Test of your SIEM
Are you using sysmon in your environment and detect unwanted behaviour from within your SIEM with it? Then have a check at sbousseaden/EVTX-ATTACK-SAMPLES and test your SIEM capabilities or create new usecases with the 120 available samples of various attack samples.
A big thanks to sbousseaden for this great contribution.
Week 30
Another "Lunch & Learn"
We had an excellent event within our "Lunch & Learn" this time with speakers from the German Aerospace (DLR) about the attempts they make in securing our ridiculously insecure flight communication.
A thrilling and eye opening event that created a lot of interest within the audience of my cyber colleges and me. I hope we all can make it for the "open doors" day on 21st July 2019 at the DLR.
Thank you very much for this event and the participation.
See it on LinkedIn
Week 29
Google Home Silently Captures Recordings of Domestic Violence and More
 Author Lindsay O'Donnell is writing an article at Threatpost about the same thing as of Alexa now was made public for Google's "Home".
Author Lindsay O'Donnell is writing an article at Threatpost about the same thing as of Alexa now was made public for Google's "Home".
In a Wednesday report, Dutch news outlet VRT NWS said it obtained more than one thousand recordings from a Dutch subcontractor who was hired as a “language reviewer” to transcribe recorded audio collected by Google Home and Google Assistant, and help Google better understand the accents used in the language. Out of those one thousand recordings, 153 of the conversations should never have been recorded, as the wake-up command “OK Google” was clearly not given, the report said.
“VRT NWS was able to listen to more than a thousand excerpts recorded via Google Assistant,” according to the report. “In these recordings we could clearly hear addresses and other sensitive information. This made it easy for us to find the people involved and confront them with the audio recordings.”Google for its part on Thursday acknowledged that VRT NWS had obtained authentic recordings, but argued that its language experts only review around 0.2 percent of all audio snippets.
“As part of our work to develop speech technology for more languages, we partner with language experts around the world who understand the nuances and accents of a specific language,” according to David Monsees, product manager at Google Search. “These language experts review and transcribe a small set of queries to help us better understand those languages. This is a critical part of the process of building speech technology, and is necessary to creating products like the Google Assistant.”
Google did acknowledge that some audio may be recorded by Google Home or Google Assistant without the wake-up word being said, due to error.
As of my earlier writing, the "Project Alias" by BjørnKarmann had already thought of this security issue and developed a excellent device made around a Raspy PI, that plays white noise to Alexa or Home while not having heard the "wakeup word". This way, if someone is eavesdroping, he only hears garbage. Still, be deactivating the "garbage" when ever the self definable "wakeup word" was heard, the white noise is turned off and the original function is been established.
A very cool and pragmatic solution…!!! Credits and respects to Bjoern.
Week 28
Logitech keyboards and mice vulnerable to extensive cyber attacks
heise Security has a brilliant article about several devices of Logitech being vulnerable of MouseJack (CVE-2019-13055)
So checkout your devices for the orange asterisk. *
The vulnerabilities allow an attacker to eavesdrop on keystrokes from wireless keyboards. Everything an affected user types, from e-mails to passwords, is readily available to the adversary. But it gets worse: An attacker can send any command to the victim's computer if a vulnerable Logitech-device is installed. And that makes it easy to infect the computer with malicious code without the rightful owner taking notice.
These products are affected
Any Logitech device that uses the so-called Unifying radio technology is affected. Logitech has been shipping the vulnerable Unifying USB receivers with wireless keyboards and mice since 2009. Unifying is used across Logitech's product range, from inexpensive entry level devices to current high-end models. The vulnerable USB receivers are recognized by a small orange star logo.
In addition, wireless gaming products of the Lightspeed series and the Wireless Presenters R500 and Spotlight are also affected. They use related radio technology. The Presenter R400, R700 and R800, however, are not affected by the vulnerabilities described in this article.
Finding and Testing MisConfigured S3 Buckets
Rohan Chavan has a cool writing on how to establish above task at medium.com.
Finding Buckets :-
These can be done manually or by using some automated scripts such as :-
bucket_finder
Download: https://github.com/FishermansEnemy/bucket_finder
S3Scanner
Download: https://github.com/sa7mon/S3Scanner
s3-inspector
Download: https://github.com/kromtech/s3-inspector
Exploiting Android Through ADB With PhoneSploit
Your Android is M I N E ! ! !
Use shodan and search for port:5555 product:"Android Debug Bridge". By the time of this writing, I got 13220 results. Manly from Asia where the providers seem to open this service and port to the Internet per default.
Now get PhoneSploit and do any of the below:
- Access Shell on a phone
- Install an apk on a phone
- Screen record a phone
- Screen Show a picture on a phone
- Pull folders from phone to pc
- Turn the device off
- Uninstall an app
- Show real time log of device
- Dump system Info
- List all apps on a phone
- Run an app
Please bear in mind, that any such action would probably be illegal according to the lawset of the country you start the action in.
First-ever malware strain spotted abusing new DoH (DNS over HTTPS) protocol
Tat is the cool thing about a job within the cyber security. One hole is closed, another one opens up…. :-)
Read the complete article by Catalin Cimpanu for Zero Day published at ZDNet about the abusing "Godlua", a Linux DDos bot that uses DoH to hide its activity within the DNS traffic.
heisec Emailcheck
![]() is providing some simple dummy emotet mailchecks to be send to your mailaccount for testing your security equipment from there servers.
is providing some simple dummy emotet mailchecks to be send to your mailaccount for testing your security equipment from there servers.
In view of the existential threat of Emotet & Co., more and more companies regulate the reception of office files via e-mail. Some lock their reception completely; often, at a minimum, Office documents that contain macros are quarantined as a precaution, or at least marked as "potentially dangerous" to warn employees. Emotet reloads additional modules via such macro functions, which infect the computer sustainably and then drive its mischief through the entire network. With the email check from heise Security you can now send harmless test emails to test your own filters.
Upgrade Confluence NOW
As per Atlassians advisory, you should upgrade your onprem installation of confluence rather today than tomorrow.
As per Alert Logic:
Exploit code for a new vulnerability in Confluence (CVE-2019-3396) has been rapidly deployed by attackers and successfully used to breach hosts. We have observed attempts by these campaigns to execute Gandcrab ransomware on the victim hosts via PowerShell and usage of standard toolsets to avoid detection. Readers are encouraged to assess and patch their environments for this vulnerability as soon as possible.
Proof of concept code for the vulnerability was made available in the public domain on the April 10 and by the next day we were observing the first weaponized attack attempts using this new vector. This emphasizes yet again the critical nature of patching as a core component of your security protection. Don’t wait until exploit code appears in the public domain, or you are reading this blog, to react. By then it might well be too late.
Week 28
Fidelis - Deception Training
I've attended a training at Fidelis in Prague to get on top of their deception solution.
Really cool stuf I'm looking forward in deploying at some customers.
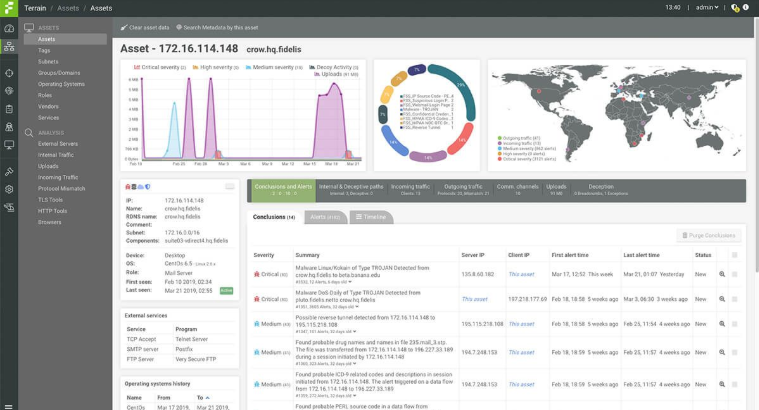
- Lure attackers with breadcrumbs on real assets to decoys and services to divert and defend
- Invoke fake users within Active Directory showing activity on decoys within deception layers
- Detect external attacks and insiders to expose reconnaissance and lateral movement
- Learn details of attack paths, resource interests and initial compromised foothold systems
Week 23
Week 21
French gas stations robbed after forgetting to change gas pump PINs

By Catalin Cimpanu for Zero Day | March 27, 2019
French authorities have arrested five men who stole over 120,000 litres (26,400 gallons) of fuel from gas stations around Paris by unlocking gas pumps using a special remote.
The five-man team operated with the help of a special remote they bought online and which could unlock a particular brand of gas pumps installed at Total gas stations.
The hack was possible because some gas station managers didn't change the gas pump's default lock code from the standard 0000. Hackers would use this simple PIN code to reset fuel prices and remove any fill-up limits.
Crooks would operate in small teams of two to three individuals who visited gas stations at night using two vehicles.
A man in a first car would use the remote to unlock the gas station, and then a second car, usually a van, would come along seconds later to fill a giant tanker installed in the back of the vehicle with as much as 2,000 or 3,000 litres in one go.
The group advertised the fuel they stole on social media, providing a time and place where customers could come and refuel their vehicles or pick up orders for gasoline and diesel at smaller prices.
Their scheme was uncovered in April 2018, when police arrested a suspect in Sagy, a Paris suburb. The suspect was in the possession of a remote at the time of his arrest. Five men, part of the same gang, were arrested on Monday, according to Le Parisien, who first reported the scheme last November.
Win back some privacy with a cone of silence for your smart speaker

A cool HACKDAY post by Dan Maloney after my collegue brought up an related posting doing the same with Arduino. :-)
To quote the greatest philosopher of the 20th century: “The future ain’t what it used to be.” Take personal assistants such as Amazon Echo and Google Home. When first predicted by sci-fi writers, the idea of instant access to the sum total of human knowledge with a few utterances seemed like a no-brainer; who wouldn’t want that? But now that such things are a reality, having something listening to you all the time and potentially reporting everything it hears back to some faceless corporate monolith is unnerving, to say the least.
There’s a fix for that, though, with this cone of silence for your smart speaker. Dubbed “Project Alias” by [BjørnKarmann], the device consists of a Raspberry Pi with a couple of microphones and speakers inside a 3D-printed case. The Pi is programmed to emit white noise from its speakers directly into the microphones of the Echo or Home over which it sits, masking out the sounds in the room while simultaneously listening for a hot-word. It then mutes the white noise, plays a clip of either “Hey Google” or “Alexa” to wake the device up, and then business proceeds as usual. The bonus here is that the hot-word is customizable, so that in addition to winning back a measure of privacy, all the [Alexas] in your life can get their names back too. The video below shows people interacting with devices named [Doris], [Marvin], [Petey], and for some reason, [Milkshake].
We really like this idea, and the fact that no modifications are needed to the smart speaker is pretty slick, as is the fact that with a few simple changes to the code and the print files it can be used with any smart speaker. And some degree of privacy from the AI that we know is always listening through these things is no small comfort either.
Posted in Raspberry Pi, Security Hacks
Malicious applications in circulation! (GanCrab 5.2)

by Hannah Kreyenberg | May 8, 2019 | Security Informationen
Original post in German translatet via google translate and put in italcs
Disguised as a professionally designed application mail with an encrypted attachment, an unidentified virus is spreading. This is reported by the Hornetsecurity Security Lab.
Look for emails with the subject "Apply for your job advertisement" or "Apply for the current job advertisement" and an attachment that is encrypted. To open the document, a password will be included in the cover letter of the e-mail. Through the encrypted .pdf, .doc or zip file, cyber criminals try to circumvent local virus scanners because the contained malicious code is thereby "hidden". However, decoding the attachment unloads the virus and infects the computer system.
In order to raise trust with the recipient of this e-mail, a good quality candidate image is often added and referred to the company's website where the alleged candidate has found the vacancy.
As the security researchers from the Hornetsecurity Security Lab now discovered, the spreading malware is a new Gandcrab campaign. Already in January this year and autumn 2018 security experts observed an increased occurrence of this type of malware. The perfidious thing about the spam wave, however, is the encrypted document that downloads the GandCrab Ransomware. The encryption leverages classic checks from the macro code, since a static analysis of the document is not possible. So the encrypted file could not be recognized by any classic anti-virus program.
As soon as the recipient opens and decrypts the attached document, the user is prompted to click the "Enable editing" and "Activate content" buttons. If you do this, the macro in the Office document starts a hidden terminal and runs PowerShell commands to download and run the GandCrab Ransomware from the Internet.
Subsequently, the GandCrab Ransomware encrypts all data on the infected machine and replaces the desktop background with a claim message.
Summary of the key data of the defective e-mail:
Cover letter is written in good German, with professional-looking details of the "applicant"
-The attachment contains an encrypted document in .pdf, .doc or zip format
-The password for decrypting the attachment is also sent in the same e-mail
-The linguistic idiom varies with the sample mail below
IoCs – SHA256:
d17646f0eb60e8844959480ef9a57eb38efc8cd55775d5585510d4df4cde29b7 (application/msword)
93e5705c467d4b92a2a1dde1c1216472e127787b58feb45804b83087b68125ad (application/msword)
Hannah did an excellent post explaining GandCrab in more detail. Below IOCs are taken from that post.
machustonecadunfe.info
316532969.doc (CDFV2 Encrypted)
SHA256 2addae338445a427cf2dfb7e486d130f6fe863506ba7a715af9e87cbf83b0978
word1.tmp (PE32 executable (GUI) Intel 80386, for MS Windows)
SHA256 9b7229403e4729d9347d2d66a4dc6a75fd87a646cbb1027d2857b066a3bbb354
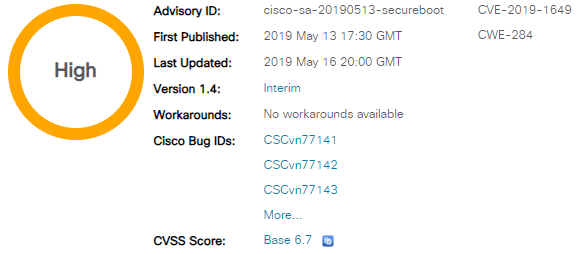
Thrangrycat 0Day: Cisco Secure Boot Hardware Tampering Vulnerability
Details
-
An attacker will need to fulfil all the following conditions to attempt to exploit this vulnerability:
- Have privileged administrative access to the device.
- Be able to access the underlying operating system running on the device; this can be achieved either by using a supported, documented mechanism or by exploiting another vulnerability that would provide an attacker with such access.
- Develop or have access to a platform-specific exploit. An attacker attempting to exploit this vulnerability across multiple affected platforms would need to research each one of those platforms and then develop a platform-specific exploit. Although the research process could be reused across different platforms, an exploit developed for a given hardware platform is unlikely to work on a different hardware platform.
Affected products: See this link
Workarounds
-
There are no workarounds that address this vulnerability.
China Chopper Malware affecting SharePoint Servers
Number: AL19-006
Date: 23 April 2019
Assessment
The Cyber Centre is aware of a campaign that is currently compromising several versions of Microsoft SharePoint Server in order to deploy the China Chopper web shell. Trusted researchers have identified compromised systems belonging to the academic, utility, heavy industry, manufacturing and technology sectors. The following versions of Microsoft SharePoint are known to be affected:
- Microsoft SharePoint Enterprise Server 2016
- Microsoft SharePoint Foundation 2013 SP1
- Microsoft SharePoint Server 2010 SP2
- Microsoft SharePoint Server 2019
It is likely that the current campaign is leveraging CVE-2019-0604 in order to deploy the web shell. Microsoft released security updates addressing this vulnerability in February and March 2019; however, many systems remain outdated.
Suggested action
- All Microsoft SharePoint Server installations should be patched with the latest security update, dated 12 March 2019, using Microsoft Update, the Microsoft Update Catalog or the Microsoft Download Center.
- If a SharePoint instance serves strictly as an on-premises solution, ensure that the server has no exposure to the Internet.
Indicators of compromise HASH Values
MD5 Hash: b814532d73c7e5ffd1a2533adc6cfcf8
SHA1 Hash: dc8e7b7de41cac9ded920c41b272c885e1aec279
SHA256 Hash: 05108ac3c3d708977f2d679bfa6d2eaf63b371e66428018a68efce4b6a45b4b4
Filename: pay.aspx
MD5 Hash: 708544104809ef2776ddc56e04d27ab1
SHA1 Hash: f0fb0f7553390f203669e53abc16b15e729e5c6f
SHA256 Hash: b560c3b9b672f42a005bdeae79eb91dfb0dec8dc04bea51f38731692bc995688
MD5 Hash: 0eebeef32a8f676a1717f134f114c8bd
SHA1 Hash: 4c3b262b4134366ad0a67b1a2d6378da428d712b
SHA256 Hash: 7d6812947e7eafa8a4cce84b531f8077f7434dbed4ccdaca64225d1b6a0e8604
Filename: stylecss.aspx
IP Address
114.25.219.100
References
Microsoft advisory: https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-0604
ZDI article: https://www.zerodayinitiative.com/blog/2019/3/13/cve-2019-0604-details-of-a-microsoft-sharepoint-rce-vulnerability
Chine Chopper information: https://cyber.gc.ca/en/guidance/web-shells-china-chopper
CVE-2018-12130 ZombieLoad-Attack
Another side channel attack has been discovered
ZDNet has done a post among many others.
And Intel has done an official post about their impacts.
Under certain conditions, data in microarchitectural structures that the currently-running software does not have permission to access may be speculatively accessed by faulting or assisting load or store operations. This does not result in incorrect program execution because these operations never complete, and their results are never returned to software. However, software may be able to forward this speculative-only data to a side channel disclosure gadget in a way that potentially allows malicious actors to infer the data.
Mitigation
Some current processors and future processors will have microarchitectural data sampling methods mitigated in the hardware. For processors that are affected, the mitigation for microarchitectural data sampling issues includes overwriting store buffers, fill buffers, and load ports before transitioning to possibly less-privileged code.
There are two methods to clear microarchitectural structures affected by MDS: MD_CLEARfunctionality1 and software sequences. On processors that enumerate MD_CLEAR2, developers can use the VERW instruction or L1D_FLUSH command3 to cause the processor to overwrite buffer values that are affected by MDS, as these instructions are preferred to the software sequences.
Panama Citizens Massive Data Breach

SECURITY DISCOVERY POSTED BY: BOB DIACHENKO MAY 13, 2019 is writing a post of:
On May 10th I identified a massive bulk of data sitting in an unprotected and publicly available Elasticsearch cluster (hence visible in any browser).

This database contained 3,427,396 records with detailed information on Panamanian citizens (labeled as ‘patients‘), plus 468,086 records with records labeled as ‘test-patient‘ (although, this data also appeared to be valid and not purely test data).
Each record contained the following info:
- full name
- date of birth
- national ID number (cedula)
- medical insurance number
- phone
- address
- other info
With Panama’s total population number at 4,1M, the exposed number of 3,4-4,8M records would correspond to almost 90% of the country’s citizens.
I have immediately sent a notification alert to CERT Panama, and within 48 hours the database has been secured.
According to Shodan historical data, the IP in question has been indexed since April 24th, 2019 and it is unknown whether anyone else has accessed the data.
The danger of having an exposed Elasticsearch or similar NoSql databases is huge. I have previously reported that the lack of authentication allowed the installation of malware or ransomware on the MongoDB servers. The public configuration allows the possibility of cybercriminals to manage the whole system with full administrative privileges. Once the malware is in place criminals could remotely access the server resources and even launch a code execution to steal or completely destroy any saved data the server contains.
TheGuardian: WhatsApp hack
As recently reported by the Guardian and many others, there is another vulnerability facing the VoIP-stack of WhatsUp. So your in danger of someone taking over your phone by just giving you a whatsup call.
But cure is available already. Just update to the most recent version and you're save. - Well, until they discover a new vuln - as usual. :-)
Read the original Guardian post here.
Google: A global hub for privacy engineering, in the heart of Europe
Sundar Pichai CEO of Google in Munich:
Last week at I/O, our annual developer conference in California, I shared how we’re working to build a more helpful Google for everyone. Keeping people safe online, and their information private and secure, is a big part of how we do this. We believe that privacy and safety must be equally available to everyone in the world, and we bring that to life with products that empower everyone with clear and meaningful choices around their data.
To build on that commitment, this week, we’re officially opening the Google Safety Engineering Center (GSEC) in Munich, Germany. We’re growing our operations and doubling the number of privacy engineers in Munich to more than 200 by the end of 2019, making Germany a global hub for Google’s cross-product privacy engineering efforts. The team will work hand-in-hand with privacy specialists in Google offices across Europe and globally, and the products built there will be used around the world.
It’s no accident that we’re building our privacy hub in the heart of Europe, and in a country that in many ways reflects how Europeans think about online safety, privacy and security. Many of our privacy products have been built in Munich, including Google Account, a central place where you can control your privacy when you use Google products. Today, more than 20 million people visit Google Account every day to review their settings, using tools like Privacy Checkup, which provides a quick and easy walk-through of your privacy settings.
Continue reading here.
Week 19
citycomp leak
http://snatchvwddns6zto.darknet.to/targets/citycomp.de/
http://snatchvwddns6zto.onion/targets/citycomp.de/packed/
Be careful, some of the files have been reported to have malware embedded..!!!
See my main page here.
Solutions for the GOOGLE CTF 2018 Hacking contest
Read the summary done by SEC Consult on an article originally written by Pichaya Morimoto (Security Consultant, SEC Consult Thailand) to give you an insight to last year’s Google Capture the Flag contest took place in June 2018.
WHAT IS GOOGLE CTF?
Google CTF is a hacking competition in the style of Capture-the-Flag, which has been going on for many years. Many of the questions have to do with Google’s technologies such as Android, Firebase, Angular, GCP and others. There are 5 categories of questions to solve: Crypto, Misc, Pwn, Re and Web. This article will focus about Web, which is a lot of fun.
Continue reading the whole blog here.
German Secret Service should also be allowed to search online in domestic Germany

Golem.de (Moritz Tremmel) is reporting about a new law proposal that shall allow the german secret service (BND) to be allowed to monitor and "hack" within Germany.
As the german law had only foreseen the BNDs activity on outside of Germany to protect the country of outside threats, changing this to inside the contrys activitys as well is a major change to my point of view. Especially as Germany had some historical reasons of limiting the secret service activity. - We should all remember what happend during the 2nd world war times and during the german democratic replic by germans spying on germans.
Although I have great trust in the germans legislative to create controls on such new duties of the BND, it still makes me think ...
The Social Democratic Party (SPD) already stated out that she will NOT support such action. - So vote wise
New Max Planck Institute for Cybersecurity and Privacy in Bochum
Translated from the German article:
Another decisive step has been taken in founding the Max Planck Institute for Cybersecurity and Privacy in North Rhine-Westphalia: The Joint Science Conference today (3 May 2019) approved the plans to set up the institute in Bochum.
Minister President Armin Laschet: "The decision in favor of Bochum is another award for the excellent research landscape in North Rhine-Westphalia: with the Horst Görtz Institute, the Universities of Bochum and Dortmund, a large number of innovative companies in the IT industry and a high-quality startup Scene, the region has become a renowned hotspot for IT security. The planned new institute will benefit from this with its research on key issues of the future. Bochum and the Ruhr Metropolis provide the ideal environment to explore the key cybersecurity technologies. We want to further expand and network innovative cutting-edge research 'Made in North Rhine-Westphalia'. "
"The scientific expertise available at the Bochum site creates excellent cooperation opportunities for cutting-edge research at this new Max Planck Institute," said Isabel Pfeiffer-Poensgen, Minister for Culture and Science. "The state government is committed to creating the best possible starting conditions for the new institute. The aim is to establish a center of excellence for basic research and training of young scientists in the field of cyber security and privacy. "
The focus of the new Max Planck Institute (MPI) will be on top-level, state-of-the-art research on cyber security, cryptography, IT system security and on legal, economic and social aspects of security and privacy. It aims to cover the entire spectrum from theory to data-driven to empirical research, and to network closely with external researchers in the fields of computer science, physics, mathematics, social sciences, economics and law.
As early as November 2018, the Senate of the Max Planck Society had called for the founding of a new Max Planck Institute for Cybersecurity and Privacy at the Bochum location. The next step towards founding is the special financing of a new building.
The Max Planck Society decided on the location of the new institute in Bochum in a location finding process encompassing several possible locations. The institute will eventually have six departments and twelve Max Planck research groups and an annual operating budget of around 20 million euros.
souvereign Runet
 (www.rbc.ru) of the Russian Federation and the end: what risks does the project on sovereign Runet bear
(www.rbc.ru) of the Russian Federation and the end: what risks does the project on sovereign Runet bear
Rusia will have it's "own" Internet for Russia-internal internet communication. Not to control traffic or content of the rusians, but to ensure their internal communication works even in case of global Internet outages and stay safe of outside threat.

The State Duma submitted a bill aimed at strengthening the sovereignty of the Runet. Why the document can reduce the quality of Internet access in Russia and lead to a restriction of the freedoms of users, understood RBC
The main provisions of the bill
Internet providers will have to “ensure installation” in their networks of technical means for countering threats. These funds (which are not explained in the document) should be provided to them by Roskomnadzor free of charge. In cases of threats to the integrity, stability and security of the functioning of the Internet of general use, the service may exercise centralized network management in a manner determined by the government. As specified by RBC Klishas, the procedure, terms and technical conditions for the installation of technical equipment, as well as the requirements for communication networks when using such technical equipment will be established in a sub-legal act of Roskomnadzor.
Even if there is no threat to the Runet, Roskomnadzor will block resources prohibited in Russia through the installed equipment. Now providers are doing it themselves.
The system of organizing the exchange of traffic on the territory of the country is changing completely - it must pass only through exchange points entered in a special register (the principle of its formation is not specified) and according to certain rules of Roskomnadzor (which is not specified).
Introduces the ability to deny service providers and organizers of information dissemination on the Internet (ORI, these include instant messengers, social networks, e-mail services, etc.) to connect to traffic exchange points. The refusal will follow if the operators do not comply with the requirements of Roskomnadzor or law enforcement officers (which ones - not specified).
Owners of communication lines that connect Russia with other countries; telecom operators; Individuals with an autonomous system number (combines groups of IP addresses so that the service provider can build a route for traffic); owners of traffic exchange points will be required to participate in the exercise. The position of the exercise will be set by the Russian government.
It is proposed to create a national system for obtaining information on domain names and network addresses, a registry that will duplicate the list of domain names and autonomous system numbers delegated to Russian users.
(translated via Google from rusian)
https://www.rbc.ru/technology_and_media/15/12/2018/5c13ccfc9a7947693d157b5e
DSA-2019-051: Dell SupportAssist Client Multiple Vulnerabilities
Dells "SupportAssist" client not only helps DELL but also the bad guys..!!!
Affected products:
Dell SupportAssist Client versions prior to 3.2.0.90.
Summary:
Dell SupportAssist Client has been updated to address multiple vulnerabilities which may be potentially exploited to compromise the system.
Details:
Improper Origin Validation (CVE-2019-3718)
Dell SupportAssist Client versions prior to 3.2.0.90 contain an improper origin validation vulnerability. An unauthenticated remote attacker could potentially exploit this vulnerability to attempt CSRF attacks on users of the impacted systems.
CVSSv3 Base Score: 7.6 (AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:H)
Remote Code Execution Vulnerability (CVE-2019-3719)
Dell SupportAssist Client versions prior to 3.2.0.90 contain a remote code execution vulnerability. An unauthenticated attacker, sharing the network access layer with the vulnerable system, can compromise the vulnerable system by tricking a victim user into downloading and executing arbitrary executables via SupportAssist client from attacker hosted sites.
CVSSv3 Base Score: 7.1 (AV:A/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H)
Resolution:
The following Dell SupportAssist Client release contains resolutions to these vulnerabilities:
- Dell SupportAssist Client version 3.2.0.90 and later.
Dell recommends all customers upgrade at the earliest opportunity.
Link to remedies:
Customers can download software from https://downloads.dell.com/serviceability/Catalog/SupportAssistInstaller.exe.
Credit:
Dell would like to thank John C. Hennessy-ReCar for reporting CVE-2019-3718 and Bill Demirkapi for reporting CVE-2019-3719.
New Exploits for Unsecure SAP Systems
Alert (AA19-122A)
New Exploits for Unsecure SAP Systems
Original release date: May 02, 2019 | Last revised: May 03, 2019
Although SAP systems should never ever been exposed directly to the internet as they host a massive amount of sensible data, there have been now defined a lot of vulnerabilities due to false configurations. Thanks to OPCDE (Dmitry Chastuhin and Mathieu Geli and their gatherings. When ever you are doing a SAP-pentest, you MUST this first.
Summary
The Cybersecurity and Infrastructure Security Agency (CISA) is issuing this activity alert in response to recently disclosed exploits that target unsecure configurations of SAP components. [1]
Risk
Vulnerable SAP applications can be compromised by a remote unauthenticated attacker having only network access to the system (without the need for a valid SAP user ID and password). Attackers can obtain unrestricted access to SAP systems, enabling them to compromise the platform along with all of its information, modify or extract this information or shut the system down. Order-to-Cash, Procure-to-Pay, Inventory Management, Treasury, Tax, HR & Payroll, and any other business process handled by SAP can be controlled, affecting the integrity of business information used to build the financial statements.
A person abusing this vulnerability would be able to perform critical business transactions including but not limited to:
- Creating fake vendors
- Creating fake employees
- Creating/modifying purchase orders
- Changing bank accounts
- Paying any vendor or employee
- Releasing shipments
- Changing inventory data
- Generating corrupted management reports
- Bypassing automatic business controls
A person performing any kind of fraud would be able to delete any traces or records that prove his or her actions and an action of this kind may not be detected.
A presentation at the April 2019 Operation for Community Development and Empowerment (OPCDE) cybersecurity conference describes SAP systems with unsecure configurations exposed to the internet. Typically, SAP systems are not intended to be exposed to the internet as it is an untrusted network. Malicious cyber actors can attack and compromise these unsecure systems with publicly available exploit tools, termed “10KBLAZE.” The presentation details the new exploit tools and reports on systems exposed to the internet.
SAP Gateway ACL
The SAP Gateway allows non-SAP applications to communicate with SAP applications. If SAP Gateway access control lists (ACLs) are not configured properly (e.g., gw/acl_mode = 0), anonymous users can run operating system (OS) commands.[2] According to the OPCDE presentation, about 900 U.S. internet-facing systems were detected in this vulnerable condition.
SAP Router secinfo
The SAP router is a program that helps connect SAP systems with external networks. The default secinfo configuration for a SAP Gateway allows any internal host to run OS commands anonymously. If an attacker can access a misconfigured SAP router, the router can act as an internal host and proxy the attacker’s requests, which may result in remote code execution.
According to the OPCDE presentation, 1,181 SAP routers were exposed to the internet. It is unclear if the exposed systems were confirmed to be vulnerable or were simply running the SAP router service.
SAP Message Server
SAP Message Servers act as brokers between Application Servers (AS). By default, Message Servers listen on a port 39XX and have no authentication. If an attacker can access a Message Server, they can redirect and/or execute legitimate man-in-the-middle (MITM) requests, thereby gaining credentials. Those credentials can be used to execute code or operations on AS servers (assuming the attacker can reach them). According to the OPCDE presentation, there are 693 Message Servers exposed to the internet in the United States. The Message Server ACL must be protected by the customer in all releases.
Signature
CISA worked with security researchers from Onapsis Inc.[3] to develop the following Snort signature that can be used to detect the exploits:
alert tcp $EXTERNAL_NET any -> $HOME_NET any (msg:"10KBLAZE SAP Exploit execute attempt"; flow:established,to_server; content:"|06 cb 03|"; offset:4; depth:3; content:"SAPXPG_START_XPG"; nocase; distance:0; fast_pattern; content:"37D581E3889AF16DA00A000C290099D0001"; nocase; distance:0; content:"extprog"; nocase; distance:0; sid:1; rev:1;)
CISA recommends administrators of SAP systems implement the following to mitigate the vulnerabilities included in the OPCDE presentation:
- Ensure a secure configuration of their SAP landscape.
- Restrict access to SAP Message Server.
- Review SAP Notes 1408081 and 821875. Restrict authorized hosts via ACL files on Gateways (
gw/acl_modeandsecinfo) and Message Servers (ms/acl_info).[4], [5] - Review SAP Note 1421005. Split MS internal/public:
rdisp/msserv=0 rdisp/msserv_internal=39NN. [6] - Restrict access to Message Server internal port (
tcp/39NN) to clients or the internet. - Enable Secure Network Communications (SNC) for clients.
- Review SAP Notes 1408081 and 821875. Restrict authorized hosts via ACL files on Gateways (
- Scan for exposed SAP components.
- Ensure that SAP components are not exposed to the internet.
- Remove or secure any exposed SAP components.
- [1] Comae Technologies: Operation for Community Development and Empowerment (OPCDE) Cybersecurity Conference Materials
- [2] SAP: Gateway Access Control Lists
- [3] Onapsis Inc. website
- [4] SAP Note 1408081
- [5] SAP Note 821875
- [6] SAP Note 1421005
- The onapsis Threat Report
- May 2, 2019: Initial version
Week 17
VirusTotal for investigators workshop
During the Kaspersky SAS 2019, VT had a workshop entitled "Virus Total for Investigators". For all those who could not attend personally, the slides are available for download.
The slides will amphasise the reader on:
- How to use VirusTotal Graph to visualize malware campaigns.
- How to use VirusTotal Intelligence to identify interesting malware metadata.
- How to use Yara for proactive and retroactive visibility.
Work on eliminating MS Telemetry services
Although the "deadly man-flu" keeps me off my desk, I could not resist to do at least some fevered work on this hot topic.
Enhance Autopsy with ClamAV MD5s

I had some quick win for doing forensics with Autopsy 4.0 and thought to write it down.
Week 15
been busy for a view weeks...
trimstray: Search engines for Hackers:
Some of you guys might already know, some might be new….
Search engines for Hackers:
https://censys.io/
https://www.shodan.io/
https://viz.greynoise.io/table
https://www.zoomeye.org/
https://wigle.net/
https://publicwww.com/
https://hunter.io/
https://haveibeenpwned.com/
https://pipl.com/
https://osintframework.com/
And some more I found:
http://fofa.so
http://app.binaryedge.io
http://onyphe.io
http://hackle.dev
http://nerdydata.com
http://thingful.net
http://reposify.com
http://netdb.io
http://weleakinfo.com
Pastbein:
https://www.threatcrowd.org/
https://fofa.so/
https://hackle.dev/
https://tineye.com/
https://nerdydata.com/
https://searchcode.com/
https://searchisback.com/
https://crt.sh/
https://censys.io/
https://www.shodan.io/
https://viz.greynoise.io/table
https://www.zoomeye.org/
https://wigle.net/
https://publicwww.com/
https://hunter.io/
https://haveibeenpwned.com/
https://searx.me/
https://pipl.com/
https://osintframework.com/
https://buckets.grayhatwarfare.com/
https://cxsecurity.com/
https://leakedsource.ru/
https://ghostproject.fr/m
https://www.onyphe.io/
http://urlquery.net/
http://protoxin.net/s3/
http://fotoforensics.com/
http://www.errorlevelanalysis.com/
http://www.insecam.org/
https://totalhash.cymru.com
https://hosts-file.net
http://vurldissect.co.uk/
https://networking.ringofsaturn.com/
https://www.networktotal.com/search.html
https://www.packettotal.com/
https://www.exploit-db.com/
https://psbdmp.ws/
https://paper.seebug.org/
http://code.woboq.org/
https://metacpan.org/
https://totalhash.cymru.com/
http://cybercrime-tracker.net/
http://malc0de.com/database/
https://sploitus.com/
http://atm.cybercrime-tracker.net/
https://www.maltiverse.com/search
https://urlscan.io/
https://www.wolfram.com/
https://www.inteltechniques.com/menu.html
https://search.weleakinfo.com/
http://databases.today/search.php
https://findsubdomains.com/
https://dns.coffee/
https://dnsdumpster.com/
http://intelx.io
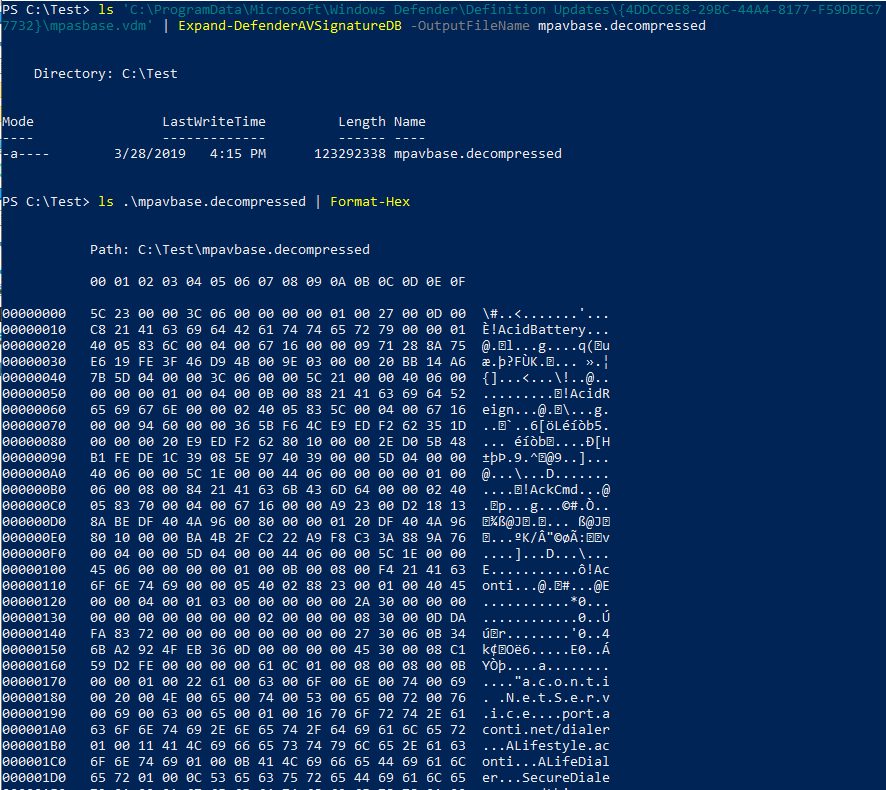
Matt Graeber: decompress WDAV .vdm files
Ever wanted to better understand how Windows Defender implements its signatures? Here's a first step. I wrote a thing to decompress WDAV .vdm files.
https://gist.github.com/mattifestation
Florian Roth: Reverse Shell Collection
Reverse Shell Collection
And a #Sigma rule to detect them
Emad Shanab: Red Team, tips,tools,methods,and more:
Complete Mandiant Offensive VM, the first full Windows-based penetration testing virtual machine distribution
For penetration testers looking for a stable and supported Linux testing platform, the industry agrees that Kali is the go-to platform. However, if you’d prefer to use Windows as an operating system, you may have noticed that a worthy platform didn’t exist. As security researchers, every one of us has probably spent hours customizing a Windows working environment at least once and we all use the same tools, utilities, and techniques during customer engagements. Therefore, maintaining a custom environment while keeping all our tool sets up-to-date can be a monotonous chore for all. Recognizing that, we have created a Windows distribution focused on supporting penetration testers and red teamers.
Born from our popular FLARE VM that focuses on reverse engineering and malware analysis, the Complete Mandiant Offensive VM (“Commando VM”) comes with automated scripts to help each of you build your own penetration testing environment and ease the process of VM provisioning and deployment. This blog post aims to discuss the features of Commando VM, installation instructions, and an example use case of the platform. Head over to the Github to find Commando VM.
Radare 3.4.0 - Codename: "hufflepuff" released
radare released this 9 days ago · 70 commits to master since this release
Release Notes
Version: 3.4.0
From: 3.3.0
To: 3.4.0
Commits: 349
Contributors: 47
Striker - Offensive Information And Vulnerability Scanner
Striker is an offensive information and vulnerability scanner.
Features
Just supply a domain name to Striker and it will automatically do the following for you:
- Check and Bypass Cloudflare
- Retrieve Server and Powered by Headers
- Fingerprint the operating system of Web Server
- Detect CMS (197+ CMSs are supported)
- Launch WPScan if target is using Wordpress
- Retrieve robots.txt
- Check if the target is a honeypot
- Port Scan with banner grabbing
- Dumps all kind of DNS records
- Generate a map for visualizing the attack surface
- Gather Emails related to the target
- Find websites hosted on the same web server
- Find hosts using google
- Crawl the website for URLs having parameters
- SQLi scan using online implemention of SQLMap (takes < 3 min.)
- Basic XSS scanning
VOOKI - Web Application Vulnerability Scanner
Vooki is a free web application vulnerability scanner. Vooki is a user-friendly tool that you can easily scan any web application and find the vulnerabilities. Vooki includes Web Application Scanner, Rest API Scanner, and reporting section.
Vooki – Web Application Scanner can help you to find the following attacks
- Sql Injection
- Command Injection
- Header Injection
- Cross site scripting – reflected,
- Cross site scripting – stored
- Cross site scripting – dom based
- Missing security headers
- Malicious JS script execution
- Using components with known vulnerabilities
- Jquery Vulnerabilites
- Angularjs Vulnerabilites
- Bootstrap Vulnerabilities
- Sensitive Information disclosure in response headers
- Sensitive Information disclosure in error messages
- Missing Server Side Validation
- Javascript Dyanamic Code Execution
- Sensitive Data Exposure
Osmedeus - Fully Automated Offensive Security Tool For Reconnaissance And
Osmedeus allow you automated run the collection of awesome tools to reconnaissance and vulnerability scanning against the target.
Features
Subdomain Scan.
- Subdomain TakeOver Scan.
- Screenshot the target.
- Basic recon like Whois, Dig info.
- IP Discovery.
- CORS Scan.
- SSL Scan.
- Headers Scan.
- Port Scan.
- Vulnerable Scan.
- Seperate workspaces to store all scan output and details logging.
- REST API.
- SPA Web UI.
- Slack notifications.
Installation
git clone https://github.com/j3ssie/Osmedeus
cd Osmedeus
./install.sh
DDoS Added Syrian Censorship logs to
- Added Syrian Censorship logs to MENA
- Added Popov alleged-Ukraine General Prosecutor offices release to State Sponsored
- Added Popov alleged-CEIEC release to State Sponsored
- Added Popov files to Researchers
- Added Pfeiffer Nuclear Weapon and National Security Archive to Researchers
- Added Identity Evropa Discord logs to to North America/United States of America
Chinese hackers poke the Bayer, but German giant says it withstood attack
![]()
Pharmaceutical brand says no data lost in Winnti outbreak
By Shaun Nichols in San Francisco 4 Apr 2019 at 22:12
German pharmaceuticals giant Bayer says it has been hit by malware, possibly from China, but that none of its intellectual property has been accessed.
On Thursday the aspirin-flingers issued a statement confirming a report from Reuters that the Winnti malware, a spyware tool associated with Chinese hacking groups, had been detected on some of its machines.
The malware was spotted on Bayer PCs in early 2018, with the company silently monitoring its behavior for more than a year before finally pulling the plug on the operation last month and notifying authorities.
continue here
Week 10
Thunderclap flaws impact how Windows, Mac, Linux handle Thunderbolt peripherals

By Catalin Cimpanu for Zero Day | February 26, 2019 -- 23:46 GMT (23:46 GMT) | Topic: Security
Windows, Mac, Linux, and FreeBSD systems are all impacted by a new vulnerability that was disclosed this week at the NDSS 2019 security conference.
The vulnerability --named Thunderclap-- affects the way Thunderbolt-based peripherals are allowed to connect and interact with these operating systems, allowing a malicious device to steal data directly from the operating system's memory, including highly sensitive information.
The research team behind this vulnerability says that "all Apple laptops and desktops produced since 2011 are vulnerable, with the exception of the 12-inch MacBook."
Similarly, "many laptops, and some desktops, designed to run Windows or Linux produced since 2016 are also affected," as long as they support Thunderbolt interfacing.
WHAT IS THUNDERBOLT?
Thunderbolt is the name of a hardware interface designed by Apple and Intel to allow the connection of external peripherals (keyboards, chargers, video projectors, network cards, etc.) to a computer.
These interfaces became wildly popular because they combined different technologies into one single cable, such as the ability to transmit DC power (for charging purposes), serial data (via PCI Express), and video output (via DisplayPort).
The technology was initially available for Apple devices but was later made available for all hardware vendors, becoming ubiquitous nowadays, especially thanks to the standard's latest version, Thunderbolt 3.
But according to the research team, all Thunderbolt versions are affected by Thunderclap. This means Thunderbolt 1 and 2 (the interface versions that use a Mini DisplayPort [MDP] connector) and Thunderbolt 3 (the one that works via USB-C ports).
Continue reading here.
The original finding was done by 
BibTeX record
@TechReport{UCAM-CL-TR-934,
author = {Rothwell, Colin L.},
title = {{Exploitation from malicious PCI Express peripherals}},
year = 2019,
month = feb,
url = {https://www.cl.cam.ac.uk/techreports/UCAM-CL-TR-934.pdf},
institution = {University of Cambridge, Computer Laboratory},
number = {UCAM-CL-TR-934}
}
Find the PoC on GitHUB done by carma
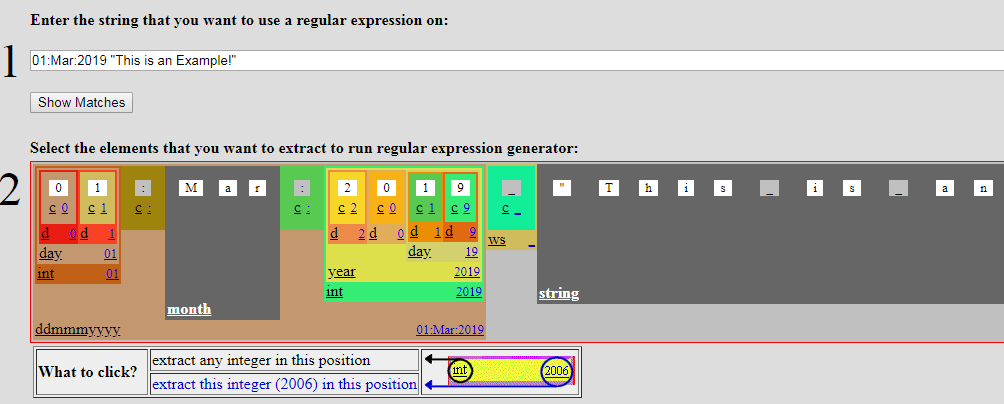
txt2re - knowing is obsolete :: regular expression generator
Some cool regex generator...
Need to escalate privileges without fancy tools?
Just for the little fun you have on foreign systems ...
Paul Seekamp (@nullenc0de) twitterte um 9:53 nachm. on Mo., Feb. 25, 2019:
Need to escalate privileges without fancy tools?
open CMD
findstr /si password *.txt
findstr /si password *.xml
dir /s pass == cred == vnc == .config
findstr /spin "password" .
reg query HKLM /f password /t REG_SZ /s
reg query HKCU /f password /t REG_SZ /s
(https://twitter.com/nullenc0de/status/1100136763157291009?s=09)
Windows Commands Abused by Attackers and their mitigation
Shusei Tomonaga from the JPCERT is providing us with some cool statistics of commonly used windows internal commands by attackers and shows a cool way of mitigation.
Hello again, this is Shusei Tomonaga from the Analysis Center.
In Windows OS, various commands (hereafter “Windows commands”) are installed by default. However, what is actually used by general users is just a small part of it. On the other hand, JPCERT/CC has observed that attackers intruding into a network also use Windows commands in order to collect information and/or to spread malware infection within the network. What is worth noting here is the gap between those Window commands used by general users and by attackers. If there is a huge difference, it would be possible to detect or limit the attackers’ behaviour by monitoring/controlling the Windows command execution.
Continue here.
Building a large scale Intrusion Detection System
The Swiss CERN is providing us with an exellent article on how to build a large scale IDS. This is really worth reading (and building) as it does not use expensive commercial LMS.

Thanks to:
Pablo Panero
CERN, Switzerland
E-mail: pablo.panero@cern.ch
Liviu Valsan
CERN, Switzerland
E-mail: liviu.valsan@cern.ch
Vincent Brillault
CERN, Switzerland
E-mail: vincent.brillault@cern.ch
Ioan Cristian Schuszter
CERN, Switzerland
E-mail: cristian.schuszter@cern.ch
In this paper the implementation of an Intrusion Detection System (IDS) both at the Network (NIDS) and Host (HIDS) level, used at CERN, is presented. The system is currently processing in real time approximately one TB of data per day, with the final goal of coping with at least 5 TB / day. In order to accomplish this goal at first an infrastructure to collect data from sources such as system logs, web server logs and the NIDS logs has been developed making use of technologies such as Apache Flume and Apache Kafka. Once the data is collected it needs to be processed in search of malicious activity: the data is consumed by Apache Spark jobs which compare in real time this data with known signatures of malicious activities. These are known as Indicators of Compromise (IoC). They are published by many security experts and centralized in a local Malware Information Sharing Platform (MISP) instance. Nonetheless, detecting an intrusion is not enough. There is a need to understand what happened and why. In order to gain knowledge on the context of the detected intrusion the data is also enriched in real time when it is passing through the pipeline. For example, DNS resolution and IP geolocation are applied to it. A system generic enough to process any kind of data in JSON format is enriching the data in order to get additional context of what is happening and finally looking for indicators of compromise to detect possible intrusions, making use of the latest technologies in the Big Data ecosystem.
Here comes the Sun (and TheHive 3.3-RC5)
New version of TheHive has been released.
On February 10, 2019, we released TheHive 3.3-RC2. It contained new features such as bulk alert merging, alert sorting, observable tag autocompletion, exporting case tags to MISP & more. Since then your favourite French code Chefs have been beesy refining TheHive 3.3 through new release candidates while getting Cortex 3 ready for prime time.
Over the weekend, Nabil decided he was not working enough already during the week. So he drained his batteries to the very last drop to release TheHive 3.3-RC5 before he crashed headfirst into his bed for a long, reparative sleep. Cumulatively since RC2, we added several features and squashed 10 bugs as described below.
Note that release candidates are beta software. You can get TheHive 3.3-RC5 from the pre-release, beta repositories. As usual, we encourage you to test it and report any bugs or issues you spot so we can address them before the final release.
Check TheHive Installation guide for further details.
Florian Roth is giving us some cool sigme detection for acount tampering detections.
Check it out here.
| Status: | |
| - '0xC0000072' # User logon to account disabled by administrator | |
| - '0xC000006F' # User logon outside authorized hours | |
| - '0xC0000070' # User logon from unauthorized workstation | |
| - '0xC0000413' # Logon Failure: The machine you are logging onto is protected by an authentication firewall. The specified account is not allowed to authenticate to the machine | |
| - '0xC000018C' # The logon request failed because the trust relationship between the primary domain and the trusted domain failed | |
| - '0xC000015B' # The user has not been granted the requested logon type (aka logon right) at this machine |
Technical Analysis: Pacha Group Deploying Undetected Cryptojacking Campaigns on Linux Servers
Introduction
Cryptomining malware, also known as cryptojacking or cryptocurrency mining malware, refers to software developed to take over a computer’s resources and use them for cryptocurrency mining without a user’s explicit permission.
There are several reports documenting this newer malware breed and how it has become more popular in the last few years.
Antd is a miner found in the wild on September 18, 2018. Recently we discovered that the authors from Antd are actively delivering newer campaigns deploying a broad number of components, most of them completely undetected and operating within compromised third party Linux servers. Furthermore, we have observed that some of the techniques implemented by this group are unconventional, and there is an element of sophistication to them. We believe the authors behind this malware are from Chinese origin. We have labeled the undetected Linux.Antd variants, Linux.GreedyAntd and classified the threat actor as Pacha Group.
Read the intire article here.
COM XSL Transformation: Bypassing Microsoft Application Control Solutions (CVE-2018-8492)
Introduction
Greetings, Everyone! It has been several months since I’ve blogged, so it seems fitting to start the New Year off with a post about two topics that I thoroughly enjoy exploring: Application Control/Application Whitelisting (AWL) and the Component Object Model (COM). As the title suggests, I stumbled upon a technique for bypassing Microsoft Application Control solutions using COM. In a particular case, the technique executes unsigned code to bypass Windows Defender Application Control (WDAC)/Device Guard, including PowerShell Constrained Language Mode (CLM) with an Extensible Stylesheet Transformation (XSLT). In this post, we will discuss the following:
- Brief Overview of Microsoft AWL Solutions
- Brief Overview of PowerShell With Constrained Language Mode
- Walkthrough of CVE-2018-8492 (WDAC Bypass via COM XSLT)
- Defensive Considerations
Read the entire article here.
while doing some forensics ...
... using Autopsy I found out, that analysing multiple data images is not suported by the program. After a while of thinking, I found the reason lyaing in the simple-sql being used with the tool that creates a deadlock when using it in analysing multiple images.
So the solution was to setup a "multi user environment" using postgres in the background.
So I started with first setting up a central repository as this wil provide the postgresql needed for the multi user as well.
See my article of setting up a central repository here.
Week 07
China: Order of the Ministry of Public Security
Did you know, that China has changed it's security law to do "security supervision" even onsite?
Chapter III Supervision and Inspection Procedures
Article XIII carry out public security organs Internet security supervision and inspection, supervision and examination can be taken on-site or remote detection manner.
Article XIV of the public security organs when conducting Internet security site supervision and inspection, the People's Police shall not be less than two, and should show people's police supervision and inspection certificate and notice above the county level people's government issued by the public security organs.
Article XV of public security organs to carry out on-site supervision and inspection of Internet security may need to take the following measures:
(1) Entering business premises, computer rooms, and workplaces;
(2) requiring the person in charge of the supervision and inspection or the network security management personnel to explain the supervision and inspection items;
(3) consulting and copying information related to Internet safety supervision and inspection items;
(4) Check the operation of technical measures for network and information security protection.
Read the complete (translated) law paper here.
Hackers KO Malta's Bank of Valletta in attempt to nick €13m

by: By Gareth Corfield 13 Feb 2019 at 17:38
In a statement reported by various local outlets, Maltese prime minister Joseph Muscat told parliament that the attack was detected shortly after the start of business today – and involved assailants, said to be from "overseas", trying to transfer €13m to a variety of banks spread across the UK, US, Czech Republic and Hong Kong.
The bank's website, BOV.com, is inaccessible at the time of writing. Even the domain's nameservers appear to have been wiped, judging from the results of multiple domain lookups attempted by The Register.
And some people still ask me why we need expensive (cyber) security at all ...
I guess the amount the damage costs would have rectified some security on the forehand.
[M.Pauli]
Distributed Denial of Secrets
Very good collection of leaks and classified documents/information.
Tor-only connection
The Collective
We are a small group, but our reach expands far beyond just our members, not all of who are listed or ever acknowledged by their own preference. We have informally worked together for many years and have developed deep connections in the field of data gathering, research, journalism, activism and technology. In 2018, we decided to pool together our expertise and time to create a unified project representing our shared goals, and provide a platform for others to know and trust.
The modern state of “leaking” organizations has detoriorated rapidly for many years, poisoned by their own egos and interests. Our view is that data is a resource and a record - this data can never tell the whole story. We trust the public to be responsible with data, and open it to them for the rigorous examination of it. In time, the truth can always emerge.
The Team
Emma Best - @NatSecGeek
Emma is an independent journalist who has spent more years filling out FOIA’s than most people have spent reading the news. Known for her tenacity in always finding the next lead and penetrating the bureaucratic walls of government, she has a keen eye for the details in every document and is a ruthless advocate for the truth even when all others dare not dig deeper.
“Vexsome” - Federal Bureau of Investigation, 2016
“The Architect”
A pseudonym for our technical behemoth who wishes to remain anonymous. He is no stranger to controversy and has been involved in privacy and technology activism for at least 10 years. The Architect is primarily responsible for advising on the operational security of the collective and maintains web and technical operations for the group.
The Firebog: The Big Blocklist Collection
While doing some work on my PiHole project, I found a enxellent collection of block lists to choose from at TheFirebog.
Have a look yourself and choose lists that best fit your needs.
Sophos KB: Resolving outbreaks of Emotet and TrickBot malware
Sophos released a good writing about EMOTET.
The basic avoidence of EMOTET infections come to:
- Secure all of your machines
- Patch early, patch often
- Block PowerShell by default
Overview
This article is designed to help Sophos customers who have detections for the Emotet or TrickBot malware. While these two malware families are different, often networks infected with one will also have the other as well. This is primarily due to Emotet spreading across a network and additionally downloading TrickBot as it goes. These two threats are very advanced and fast moving, they also use different techniques to achieve their goals and removing both of these involves taking the same actions. In this article, we cover the basic points worth knowing about these threats, how to remove them and how to improve your security to help prevent getting infected again in the future.
The following sections are covered:
MISP OSINT Feeds
MISP includes a set of public OSINT feeds in its default configuration. The feeds can be used as a source of correlations for all of your events and attributes without the need to import them directly into your system. The MISP feed system allows for fast correlation but also a for quick comparisons of the feeds against one another.
How to have my feed published in the default MISP OSINT feed
- Fork the MISP project on GitHub.
- Update the default MISP feed to add your feed(s).
- Make a pull-request with the updated JSON file.
Paul Seekamp: Secure your printers !
Paul Seekamp is giving a quick win if your printers are configured to use ldap/AD authentication to register itself within you domain.
- Log into printer.
- Look for LDAP configured.
- Point the destination to your PC.
- netcat -l -vv -p 444
- Initiate an LDAP query.
Wait for creds!
Week 06
ENISA: Excellent training material

Find some excellent technical training resources at the page of the European Union Agancy for Network and Information Security.
- Building artifact handling and analysis environment
- Processing and storing artifacts
- Artefact analysis fundamentals
- Advanced artefact handling
- Introduction to advanced artefact analysis
- Dynamic analysis of artefacts
- Static analysis of artefacts
- Forensic analysis: Local incident response
- Forensic analysis: Network incident response
- Forensic analysis: Webserver analysis
- Developing Countermeasures
- Common framework for artefact analysis
- Using indicators to enhance defence capabilities
- Identification and handling of electronic evidence
- Digital forensics
- Mobile threats incident handling
- Mobile threats incident handling (Part II)
- Proactive incident detection
- Automation in incident handling
- Introduction to network forensics New
- Honeypots
- Vulnerability handling
- Presenting, correlating and filtering various feeds
Week 05
2.2 billion passwords have been leaked and published
Check HIBP to see if you are a victim. He provides checks against 6,474,028,664 pwned account including the Collection #1 sources.
Looking forward to see the new rockyou.txt "best password dictionary"
Or get you a copy of the source "Collection #1" and search offline if you have been pwned.
"Collection #2 - #5" are already available as well, but you'd have to dig a bit deeper.
https://pastebin.com/RyWJgaED
magnet:?xt=urn:btih:B39C603C7E18DB8262067C5926E7D5EA5D20E12E&dn=Collection%201&tr=udp%3a%2f%2ftracker.coppersurfer.tk%3a6969%2fannounce&tr=udp%3a%2f%2ftracker.leechers-paradise.org%3a6969%2fannounce&tr=http%3a%2f%2ft.nyaatracker.com%3a80%2fannounce&tr=http%3a%2f%2fopentracker.xyz%3a80%2fannounce
magnet:?xt=urn:btih:D136B1ADDE531F38311FBF43FB96FC26DF1A34CD&dn=Collection%20%232-%235%20%26%20Antipublic&tr=udp%3a%2f%2ftracker.coppersurfer.tk%3a6969%2fannounce&tr=udp%3a%2f%2ftracker.leechers-paradise.org%3a6969%2fannounce&tr=http%3a%2f%2ft.nyaatracker.com%3a80%2fannounce&tr=http%3a%2f%2fopentracker.xyz%3a80%2fannounce
28th Januarry: European Data Protection Day
Even those who have "nothing to hide" should protect their privacy
January 28, 2019
They talk to a friend in a café. Suddenly, the waiter asks what your phone numbers are, who your friends are and what you are talking about. Do you provide information? Would you post the information if, in return, you did not have to pay the bill? Do you have something to hide if you do not respond to this trade?
Internet users who voluntarily disclose their privacy to free online services often do so, citing that they have "nothing to hide". However, this point of view is untenable. Having nothing to hide may be a desirable state of affairs, but it is fundamentally different from giving up your privacy.
Not informing the waiter does not mean that you have something to hide but that you want to preserve the privacy you deserve. You may be talking about something banal, but you simply do not think the matter concerns the waiter. In addition, you do not know what the waiter could do with the information or where his interest comes from.
Those who do not unknowingly disclose personal information to unknown persons in everyday life should certainly not do that towards online services. Combining different data sources makes it easy to draw a detailed picture of the users, which may reveal much more about them than they would like.
Today is the European Data Protection Day. Protect your privacy, e.g. With
Week 04
France will engage in offensive cyber warfare
I guess this will start a controverse discussion about this way of "fighting fire with fire" philosophy....
France will engage in offensive cyber warfare
French defence secretary Florence Parly announced that France will engage in a policy of using “cyber arms as all other traditional weapons… to respond and attack" (The Register).
It's a significant statement in an area that governments have often been leery of admitting to and is likely to prompt a shift in international discussion and rhetoric on cyber warfare. Meanwhile, French diplomat Jean Heilbronn has suggested that online espionage should be treated as business as usual by international governments, much as its physical equivalent currently is.
WhatApp phishing attempt from original SMS-source
A wide phishing attempt is active since the last view days. - Well this would not be worth a news, but the phishing came from the original WhatApp SMS verification number and by that looks really good.
But keep in mind, WhatApp is free and known german gramar.
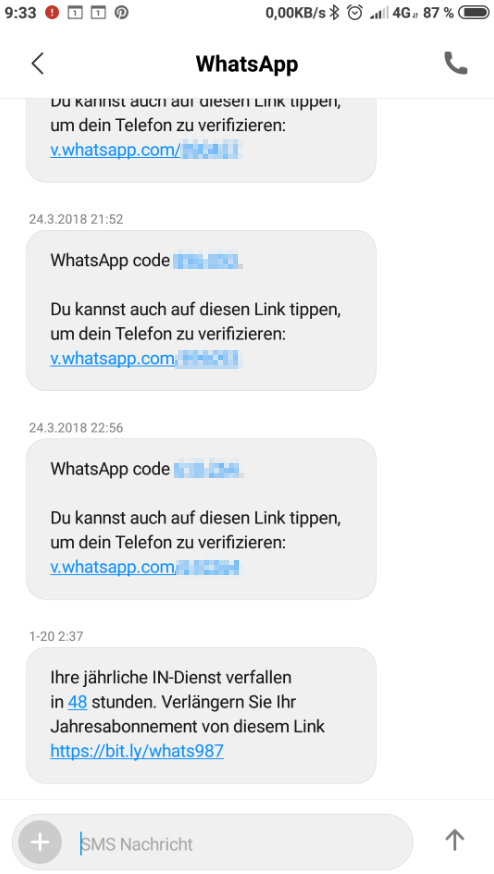
BYOB (Build Your Own Botnet)
This goes to Hugo and his investigative searching for news...
malwaredllc is giving us a complete botnet client-server setup for educational purpose. So build you own botnet and find detections and mitigations in your own lab setup.
Despite of the educational aspect of such doing, sadly the bad guys abuse this action already in the wild. Everything can be used in good and bad ways. I think A. Einstein mentioned something like that.
But as the actual source is available, it will be an excellent example for security analysts to analyse the bot and create mature detectors to alert of such activity found in your network.
So thanks malwaredllc for the contribution...!!!
BAMF (Backdoor Access Machine Farmer)
If you ever wanted to use shodan like a pro and find and use exploitable routers for education, this tool of malwaredllc is your choice.
BAMF is an open-source tool designed to leverage Shodan (a search engine for the Internet of Things) to discover vulnerable routers, then utilize detected backdoors/vulnerabilities to remotely access the router administration panel and modify the DNS server settings.
Week 03
Metasploit Framework 5.0 Released!
![]() announced the new release of Metasploit 5.0 with some cool additions.
announced the new release of Metasploit 5.0 with some cool additions.
The following is a high-level overview of Metasploit 5.0’s features and capabilities.
-
Metasploit users can now run the PostgreSQL database by itself as a RESTful service, which allows for multiple Metasploit consoles and external tools to interact with it.
-
Parallel processing of the database and regular
msfconsoleoperations improves performance by offloading some bulk operations to the database service. -
A JSON-RPC API enables users to integrate Metasploit with additional tools and languages.
-
This release adds a common web service framework to expose both the database and the automation APIs; this framework supports advanced authentication and concurrent operations. Read more about how to set up and run these new services here.
-
Adds
evasionmodule type and libraries to let users generate evasive payloads without having to install external tools. Read the research underpinning evasion modules here. Rapid7’s first evasion modules are here. -
The
metashellfeature allows users to run background sessions and interact with shell sessions without needing to upgrade to a Meterpreter session. -
External modules add Metasploit support for Python and Go in addition to Ruby.
-
Any module can target multiple hosts by setting RHOSTS to a range of IPs, or by referencing a hosts file with the
file://option. Metasploit now treats RHOST and RHOSTS as identical options. -
An updated search mechanism improves Framework start time and removes database dependency.
Passport pictures with the help of google search
If you'd need some idea of how a foreign passport looks like, just ask Dr. Google:
intitle: "Index of /" Passport
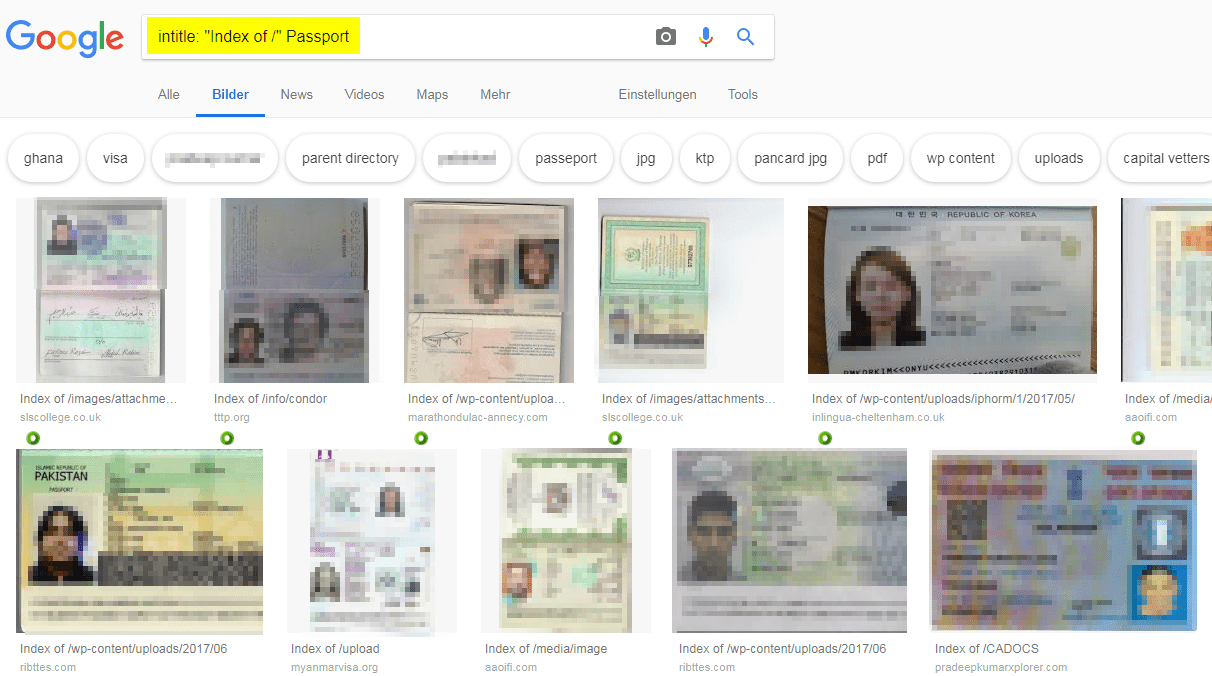
And this is not to build yourself another identitiy, this is to compare a foreign passport that is sown to you if it looks "good" or not. :-)
Week 02
A happy new year and welcome back to the exciting world of cyber related news that thrills cyber nerds and other freaks.
Twitter leak or #BTLEAK
During the end of 2018, just bevore christmas, the germany partys have got a fancy gift from santa via some tweets, promissing valuable information of several prominent politicians of the german parliament.
Although twitter, google and other bigger institutions tried their best to hide the actual information, but the network is designed to overcome an atomic desaster, so hiding is hard within an environment that never forgets.
By the time of writing, I was still able to use some caches and crawler to get me the actual information and follow the several URL's (669) within the head documents.
I'm still busy with reading and evaluating the information so far, but from the first and second sight, it looks not like the very, very finest information. But, it shows how unprofessional and childish polititians use their data.
Never the less of the quality of the information itself, it is an fantastic source of information for trust relationsships that can be used in phishing and are excellent for social engineering. I*m sure further attacks from turla etc. will use it as a valuable tool.
Some OSINT hints for #btleaks
To see how I did a "quick catch" on the BTLEAK files, have a look at my documentation of how I found the data and links although the major information was hidden and blocked.
Hacking Chromecasts/Google Homes/SmartTVs
Good hacker have showed the world that Googles Chromecast is often available via the Internet due to badly configured routers allowing UPnP, by playing a youtube video at 123141 devices.
CastHack gives a cool overview of how far they are:
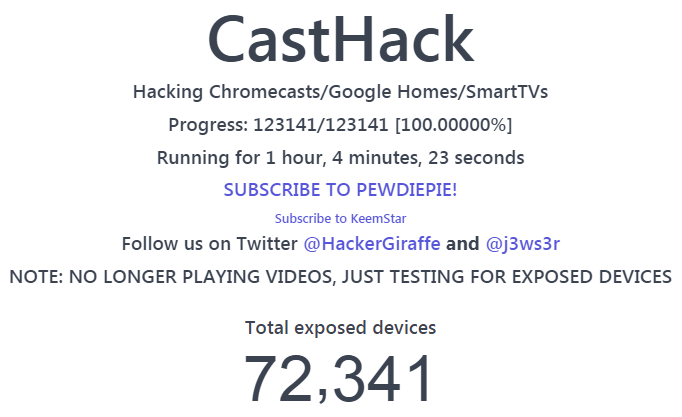




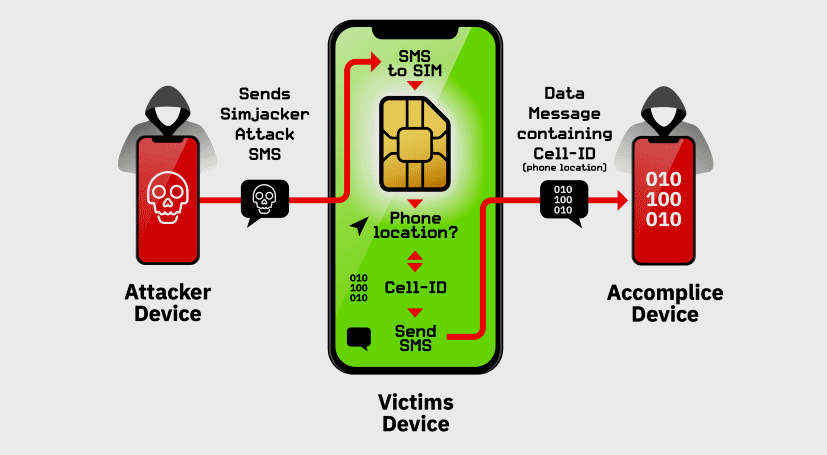
 has done a tweet about a poc of CVE-2019-15642.
has done a tweet about a poc of CVE-2019-15642.